Ssh Logging And Session Management Using Aws Ssm Toptal
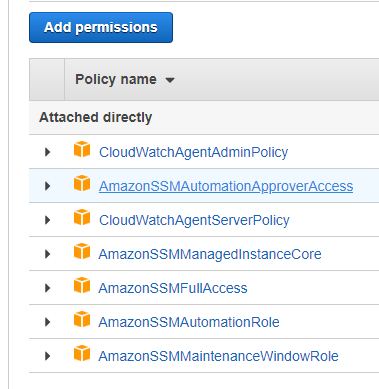
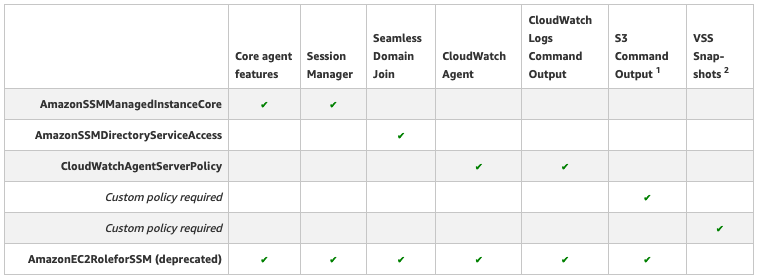
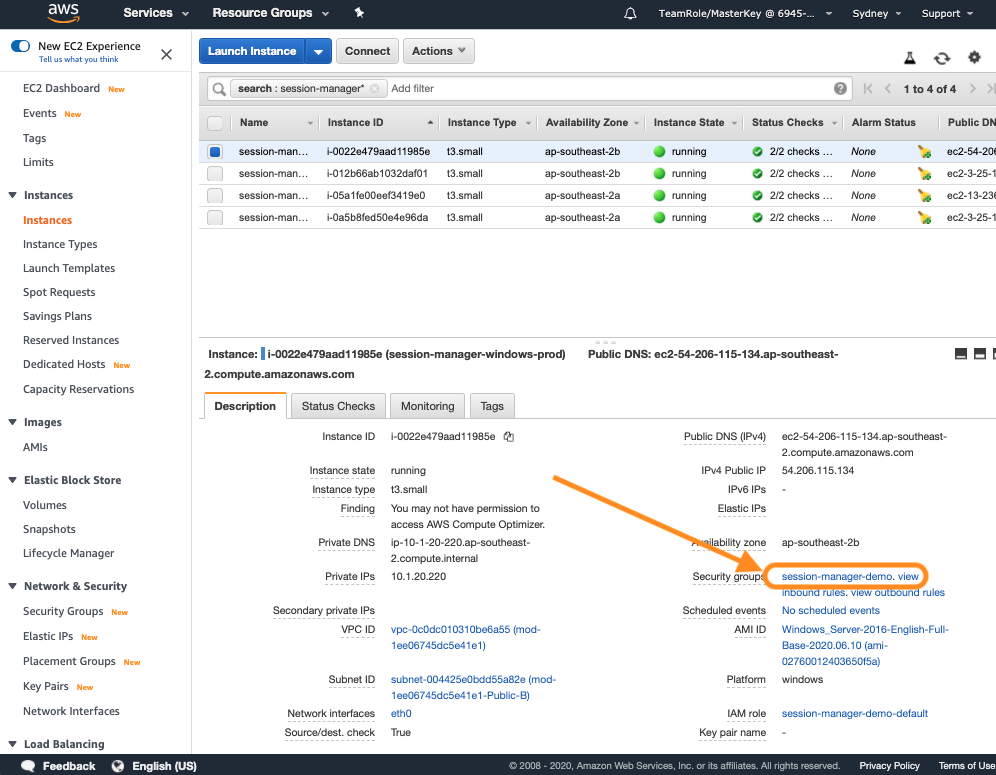
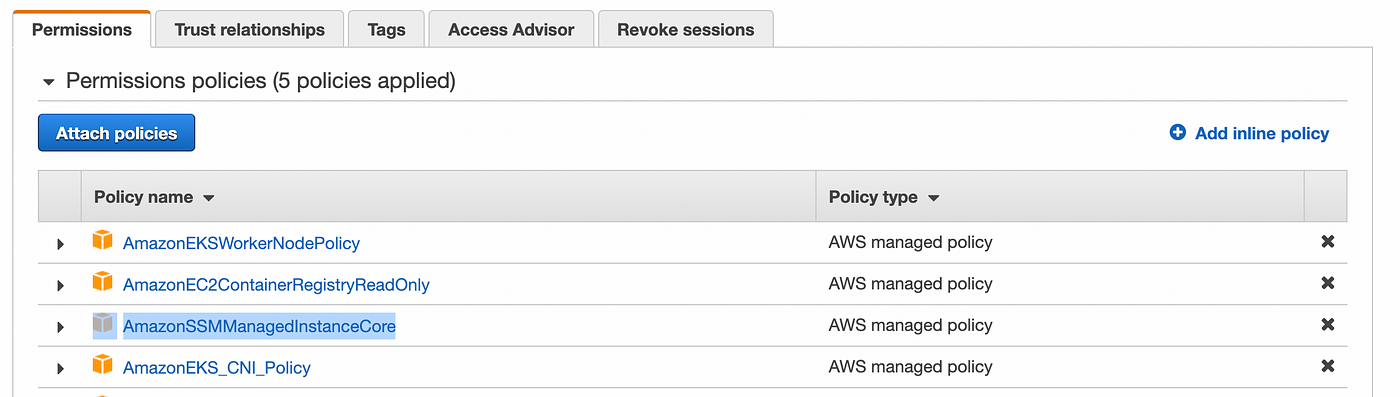
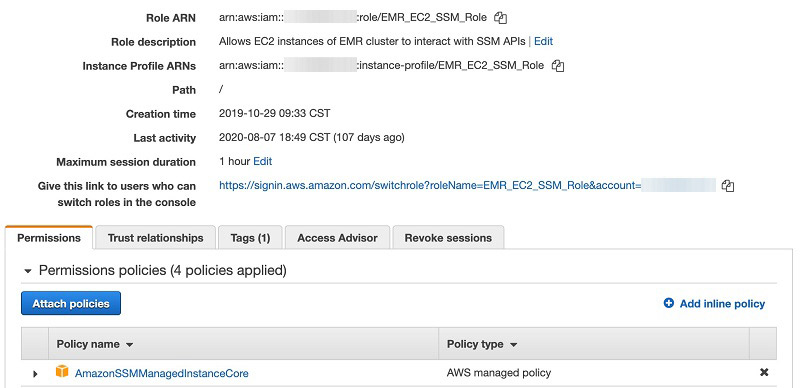
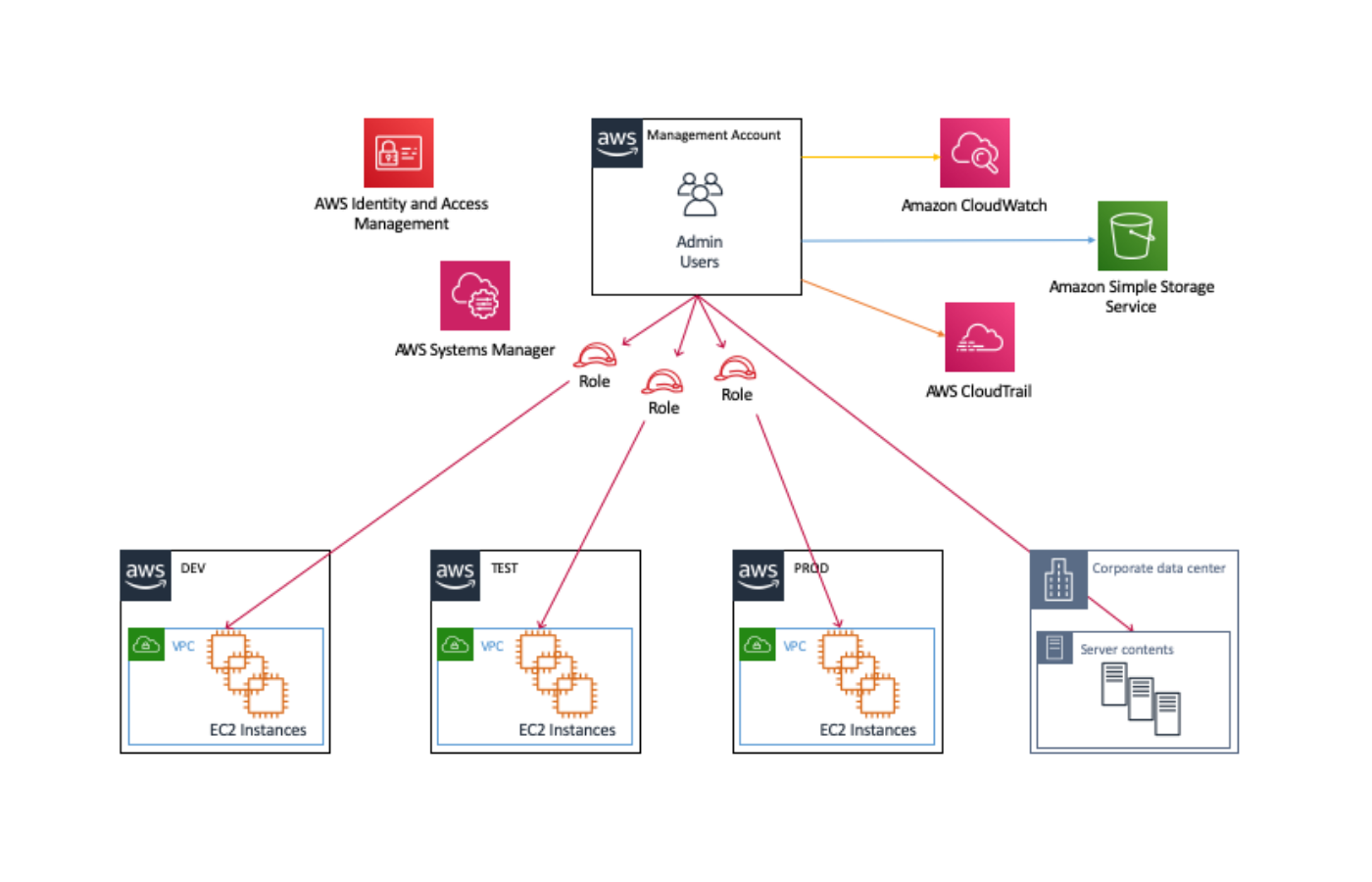
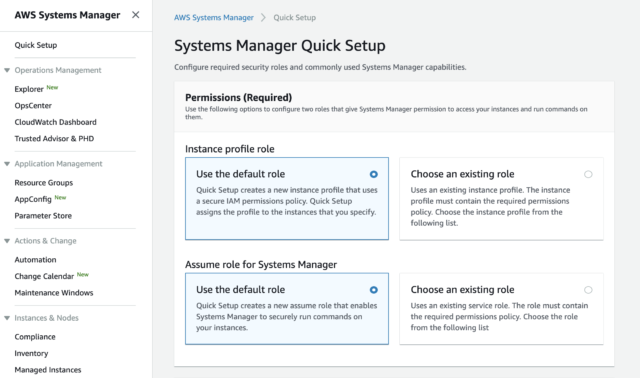
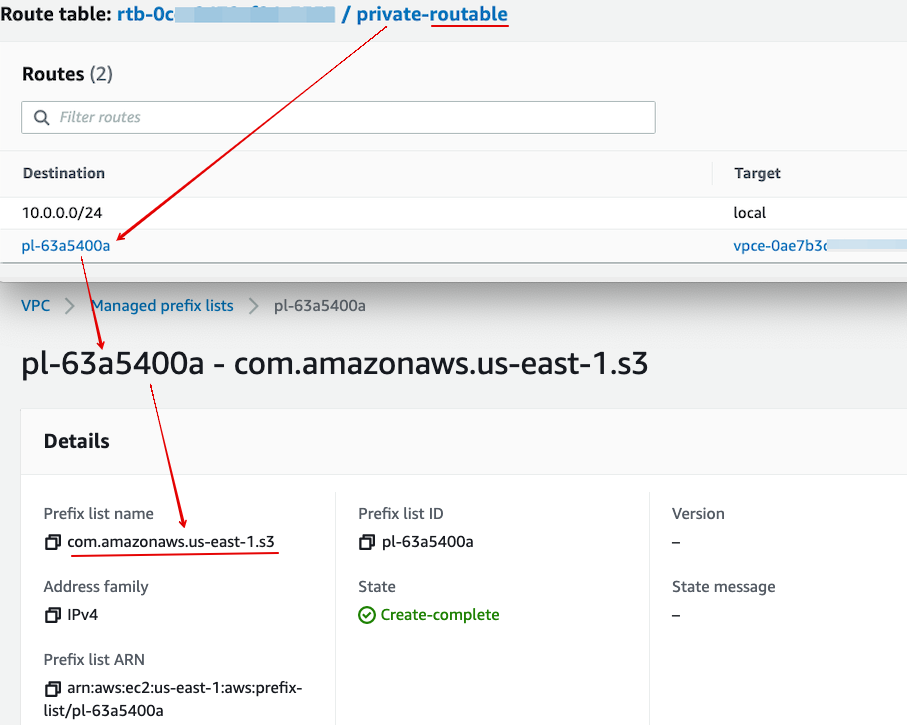
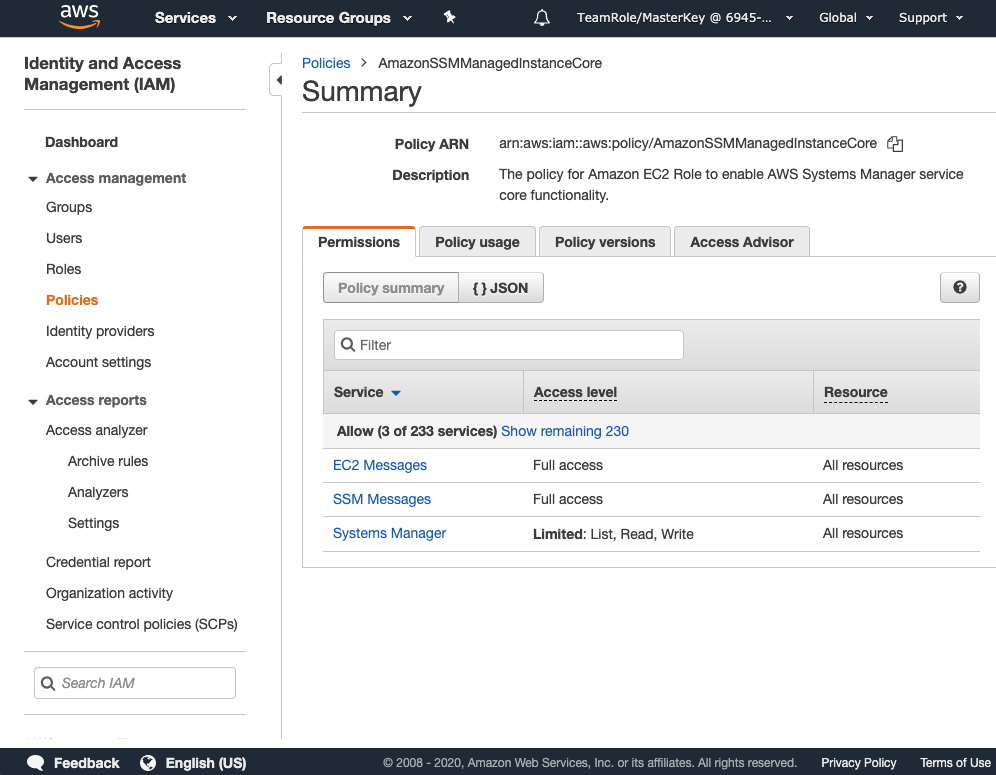
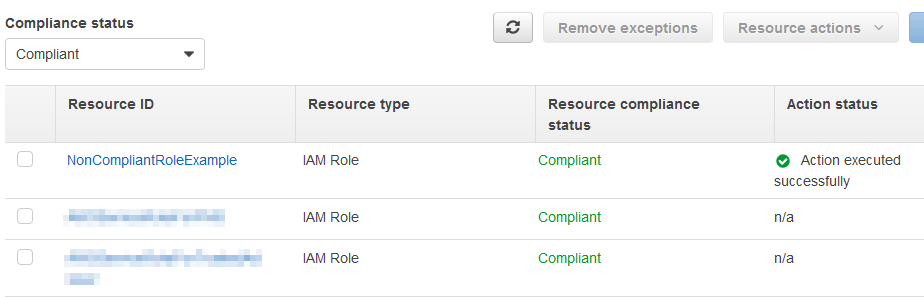
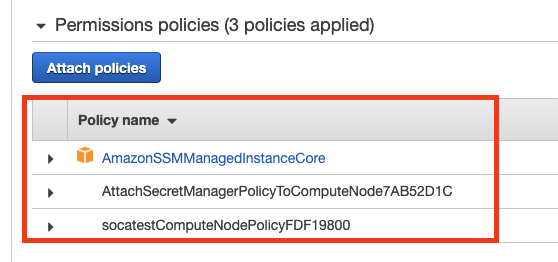
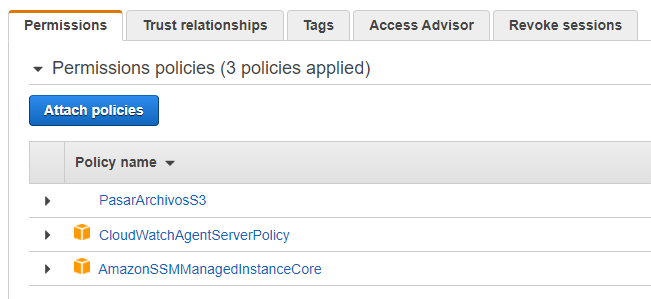
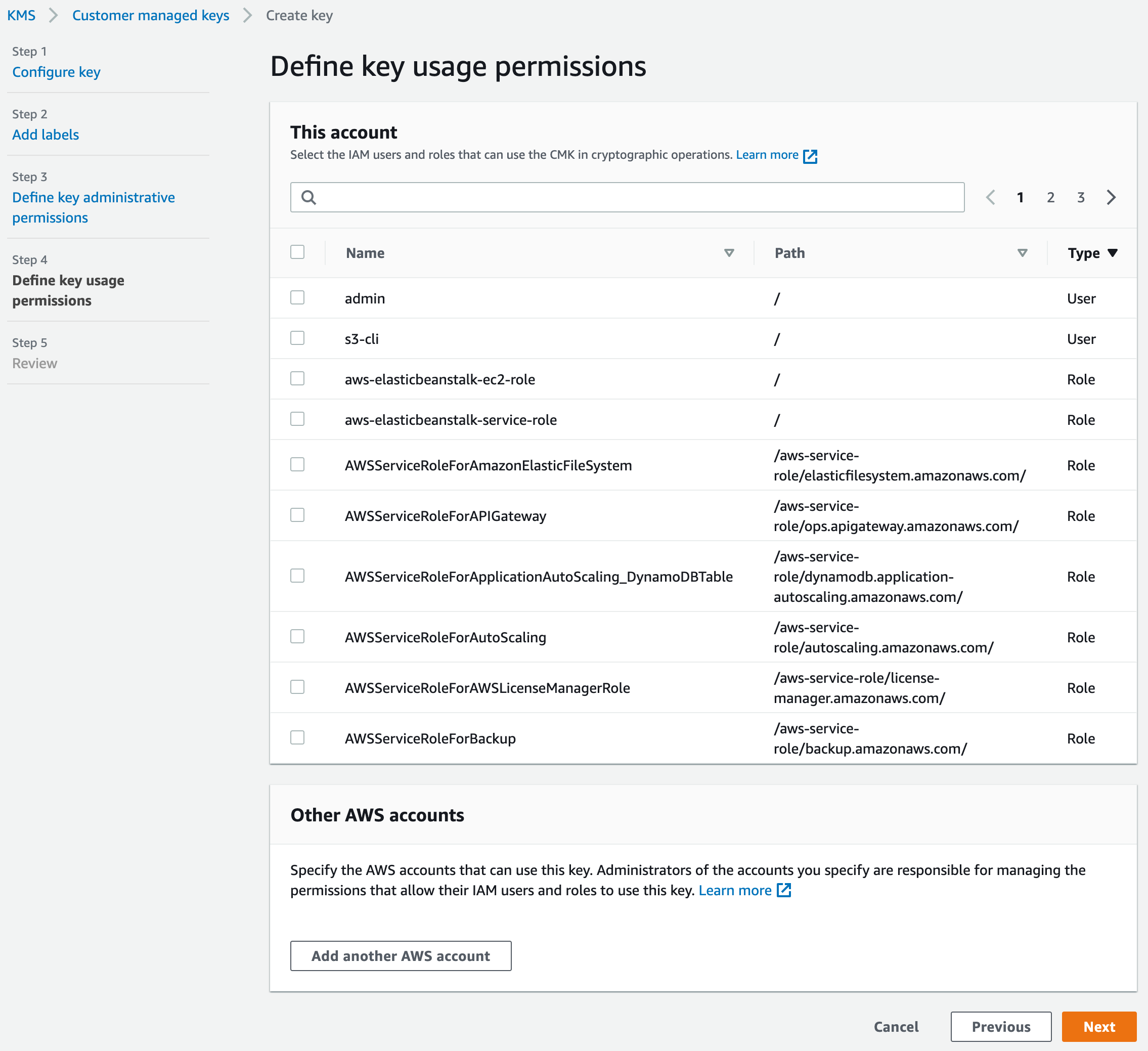
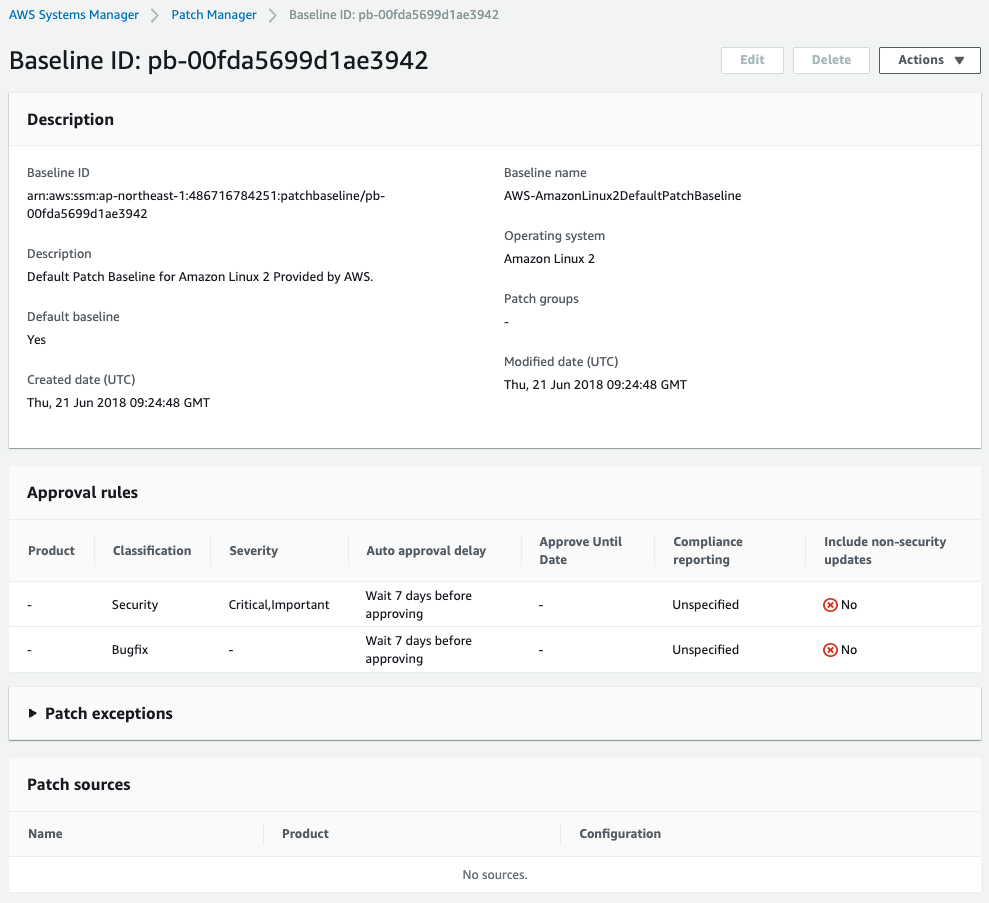
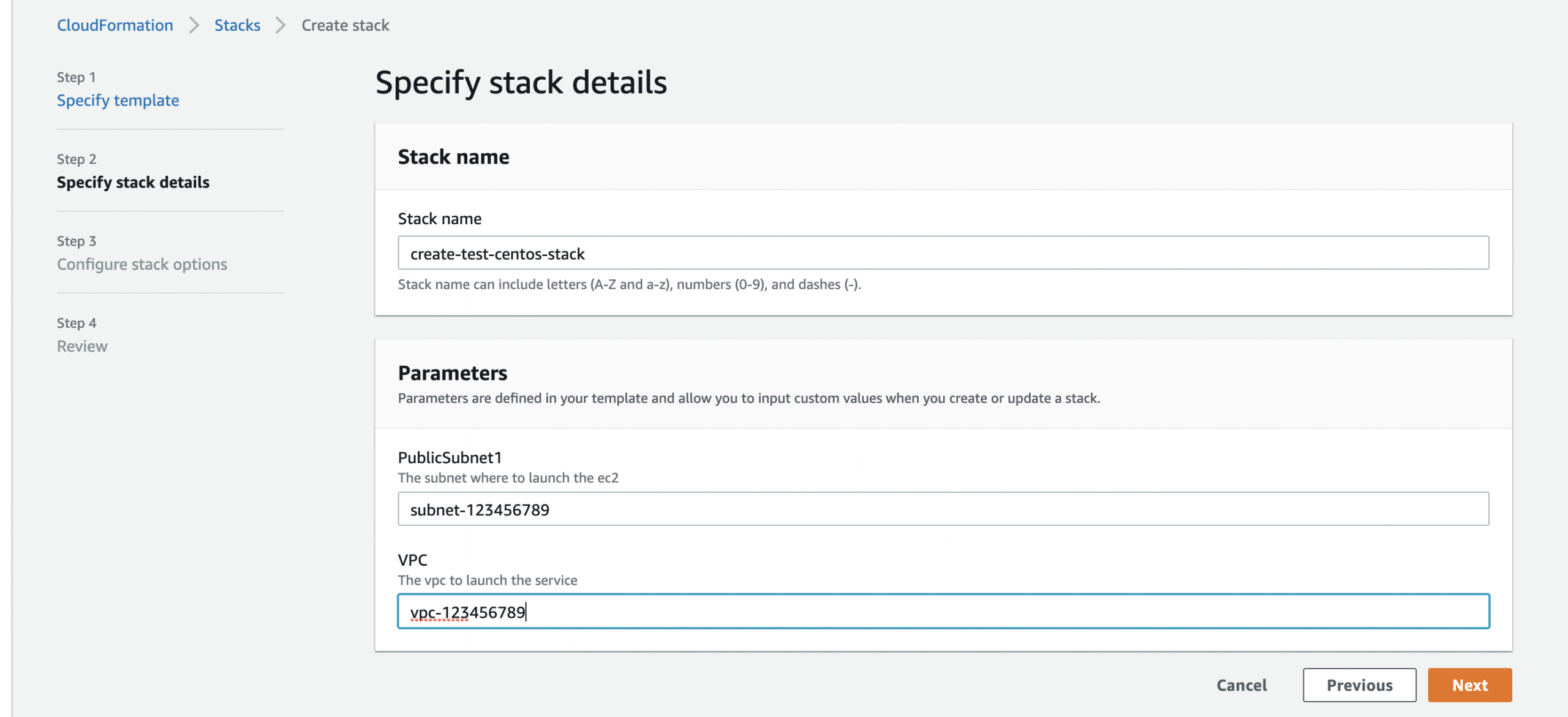
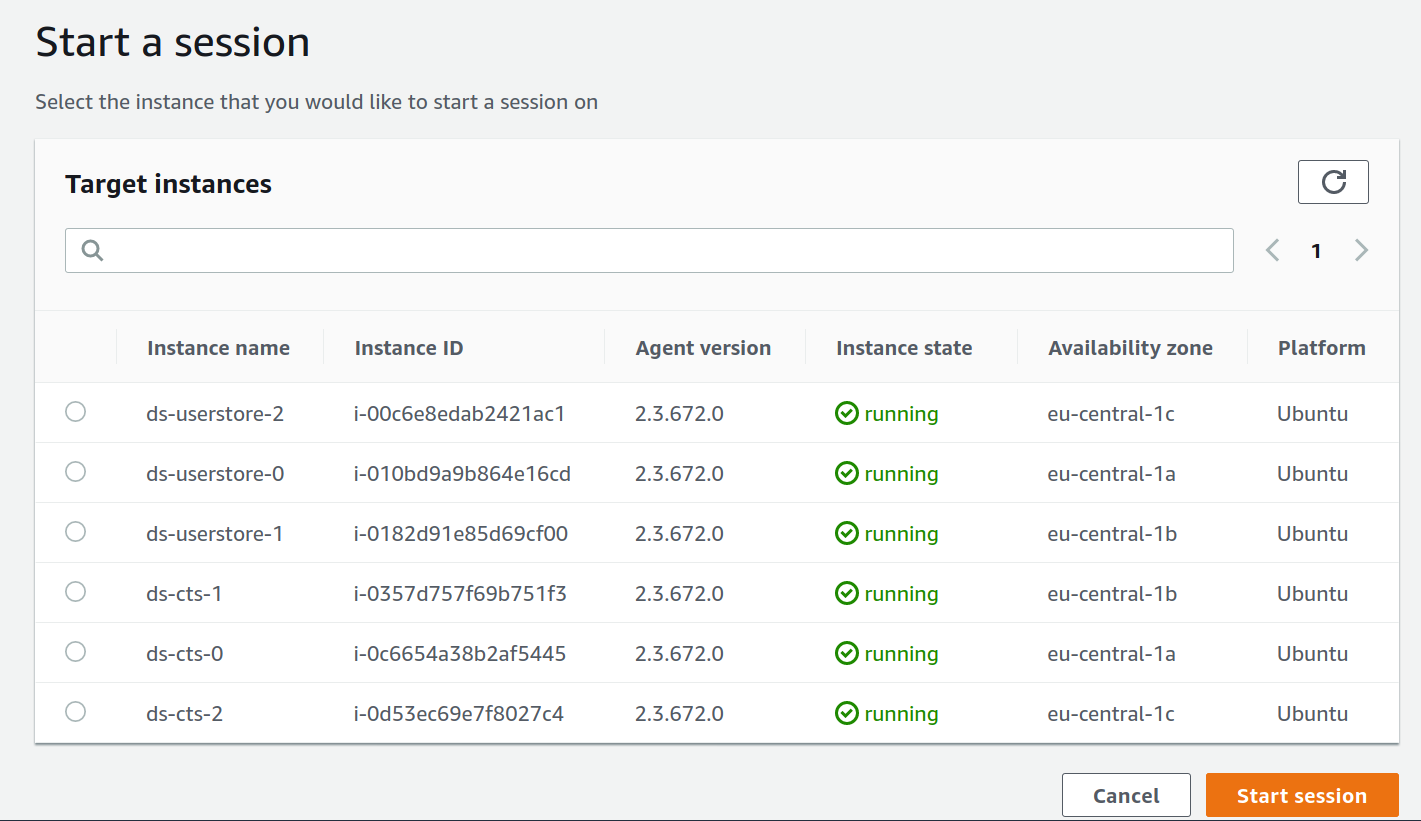
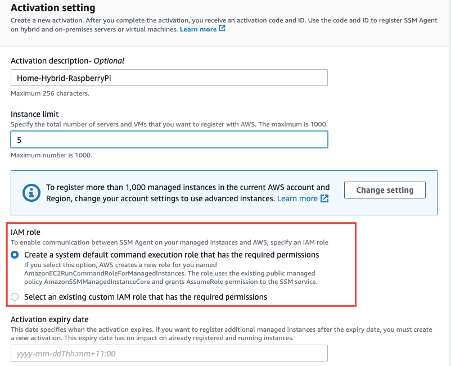
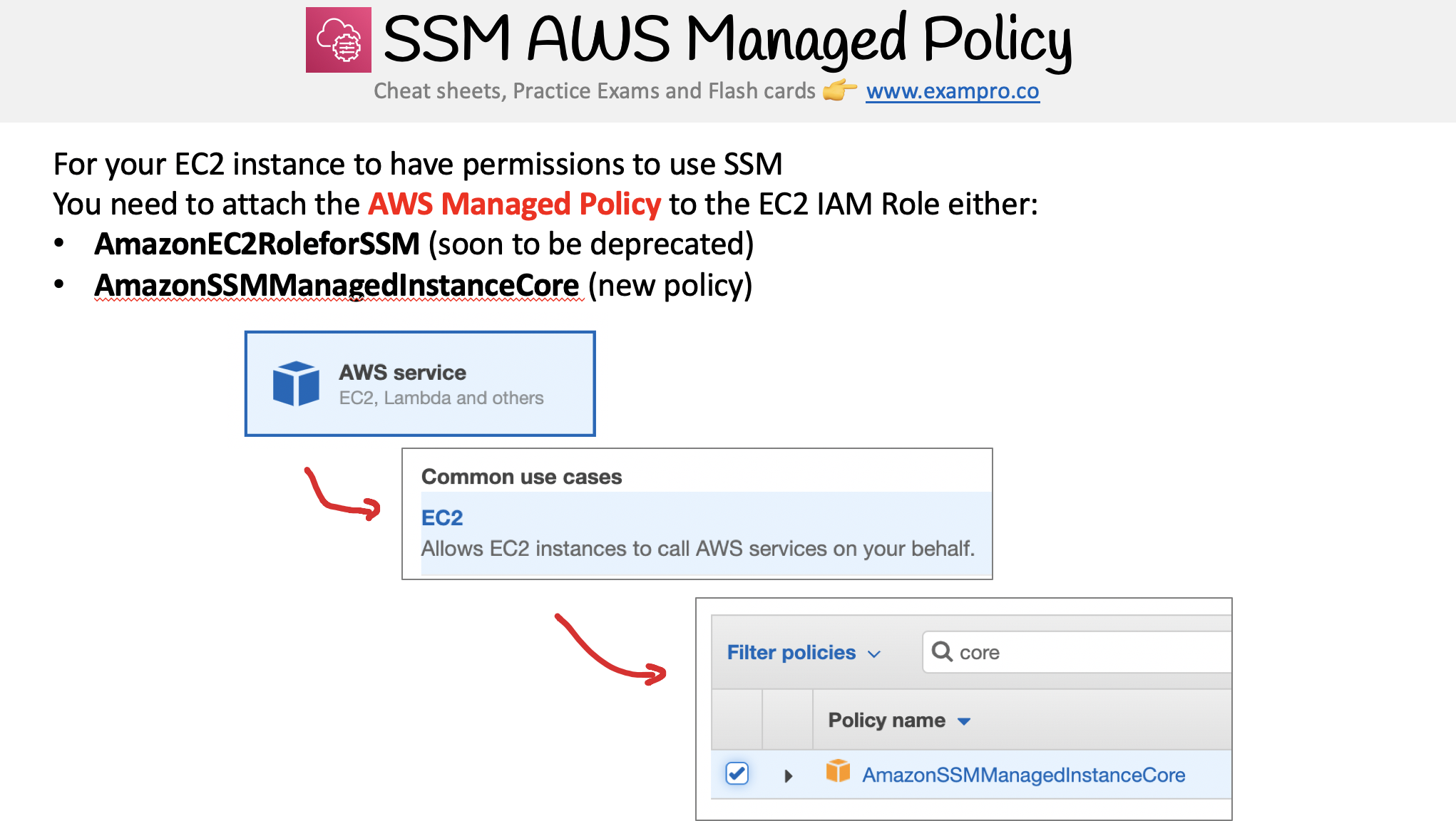
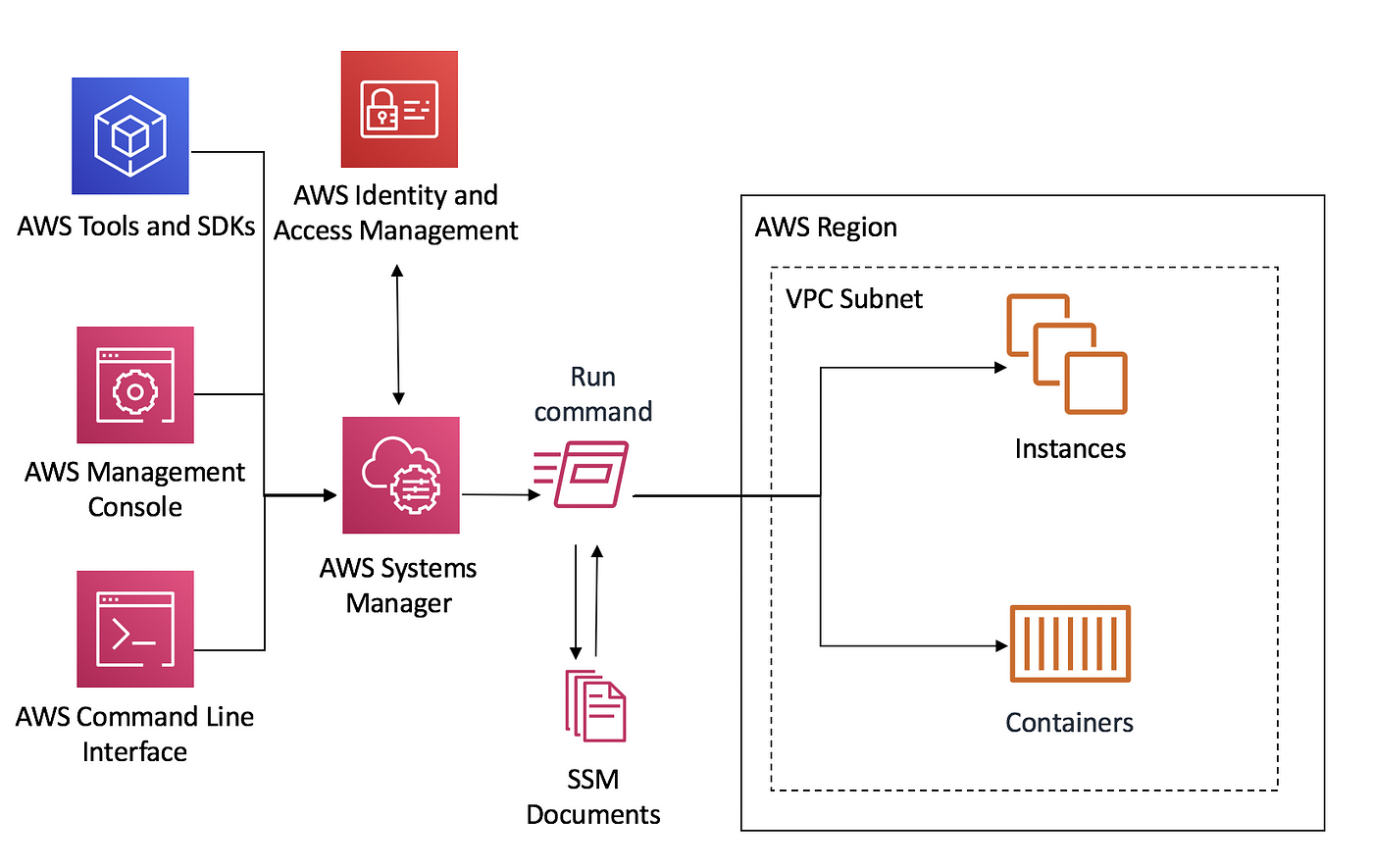
The EKS cluster will be created in the custom VPC created earlier Initiate the deployment with the following command, cdk deploy eksclusterstackAdding Session Manager permissions to an existing instance profile Follow these steps to embed Session Manager permissions in an existing AWS Identity and Access Management (IAM) instance profile that doesn't rely on the AWSprovided default policy AmazonSSMManagedInstanceCore for instance permissions This procedure assumes that your existing profile already includes
Amazonssmmanagedinstancecore permissions
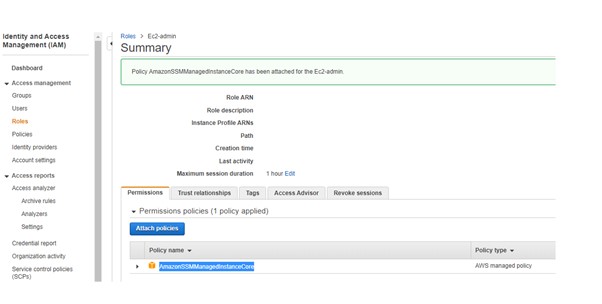
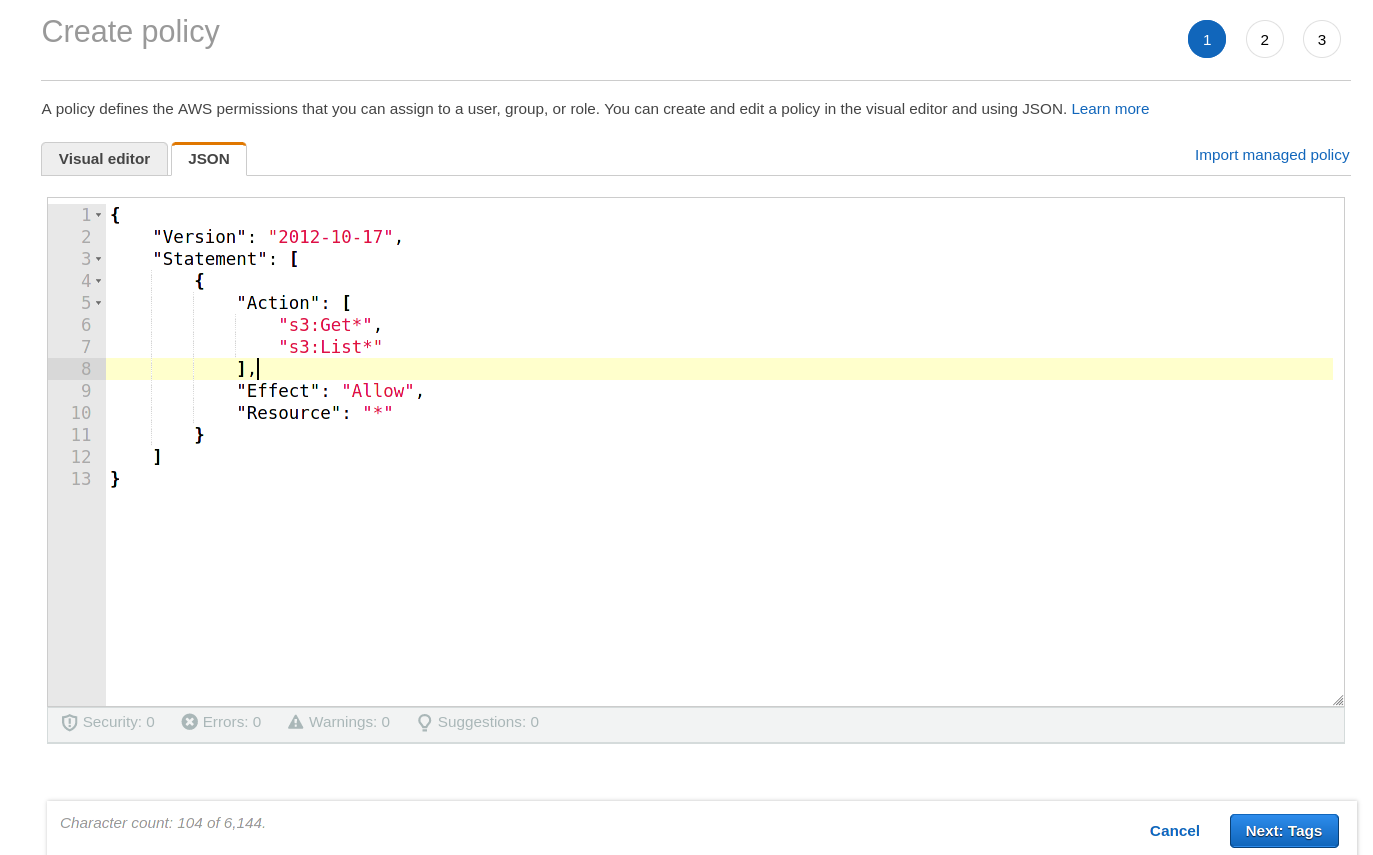
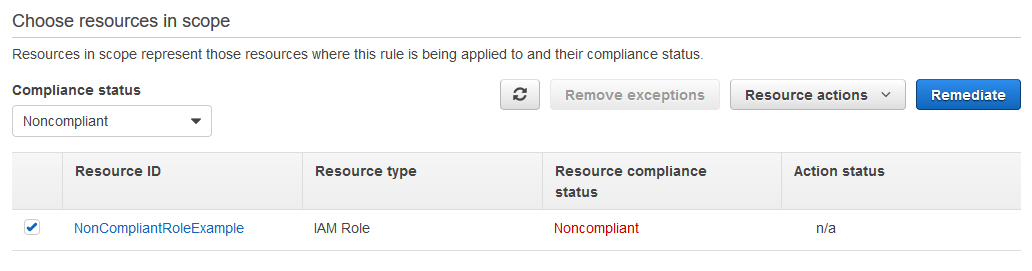
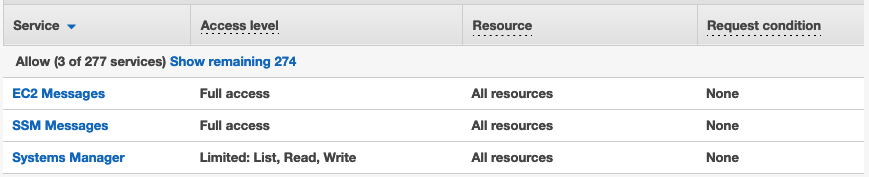
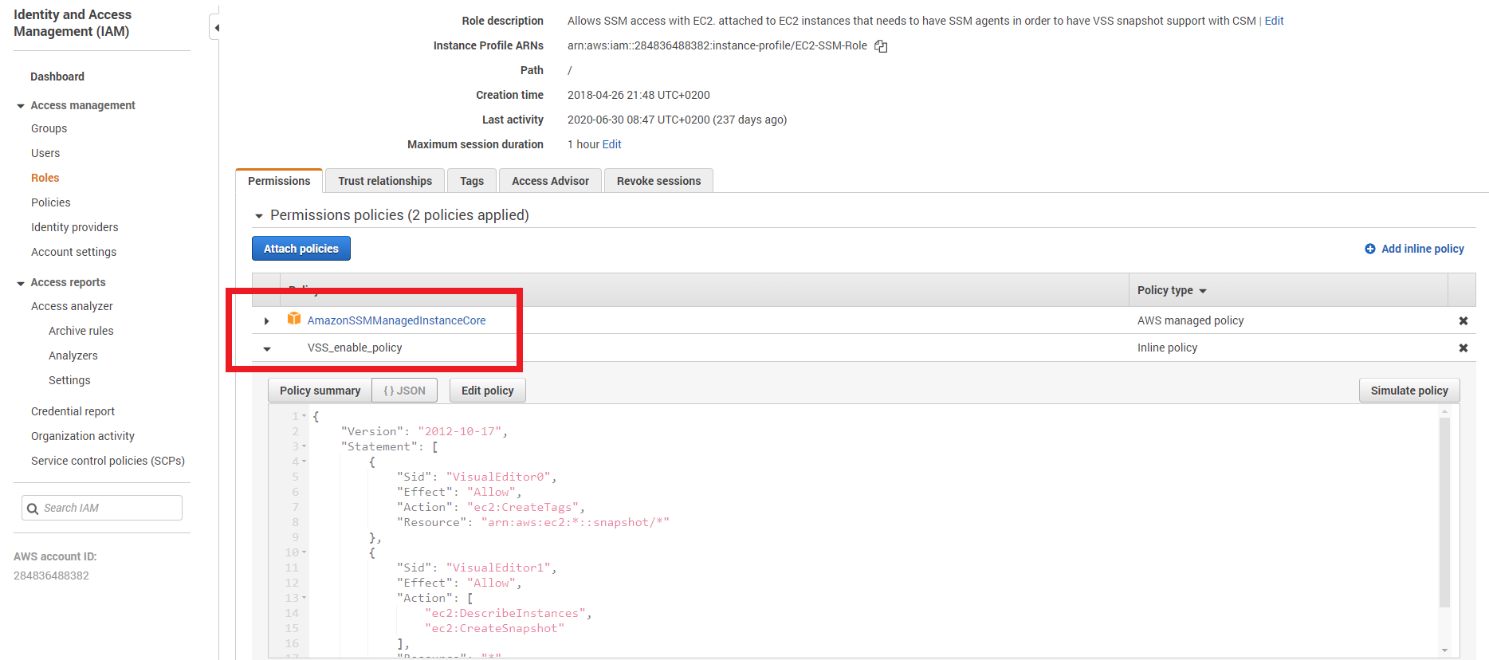
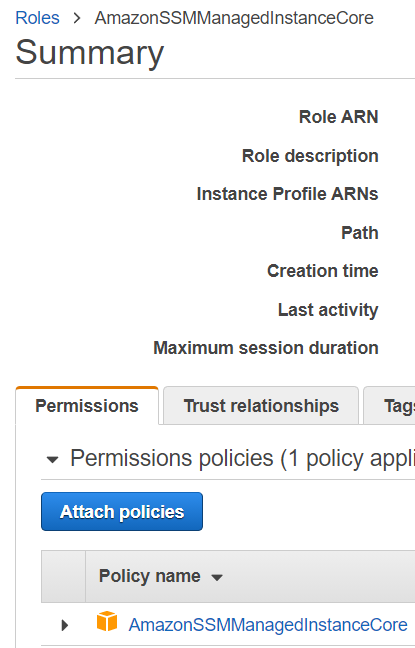
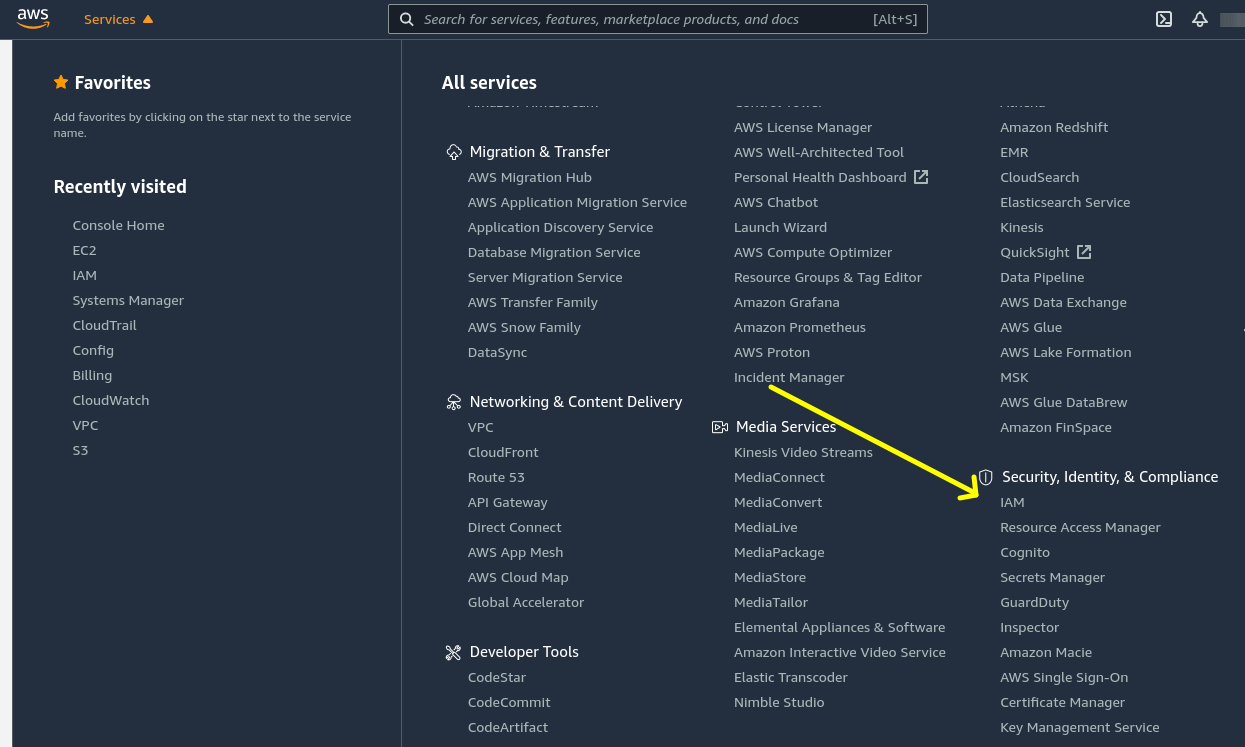
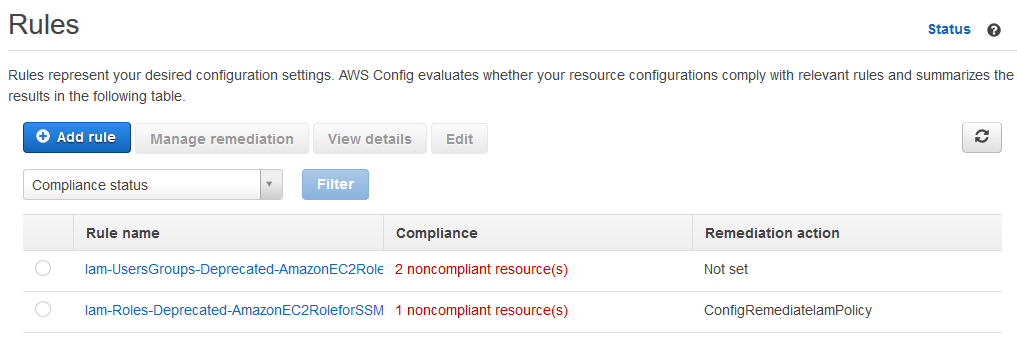
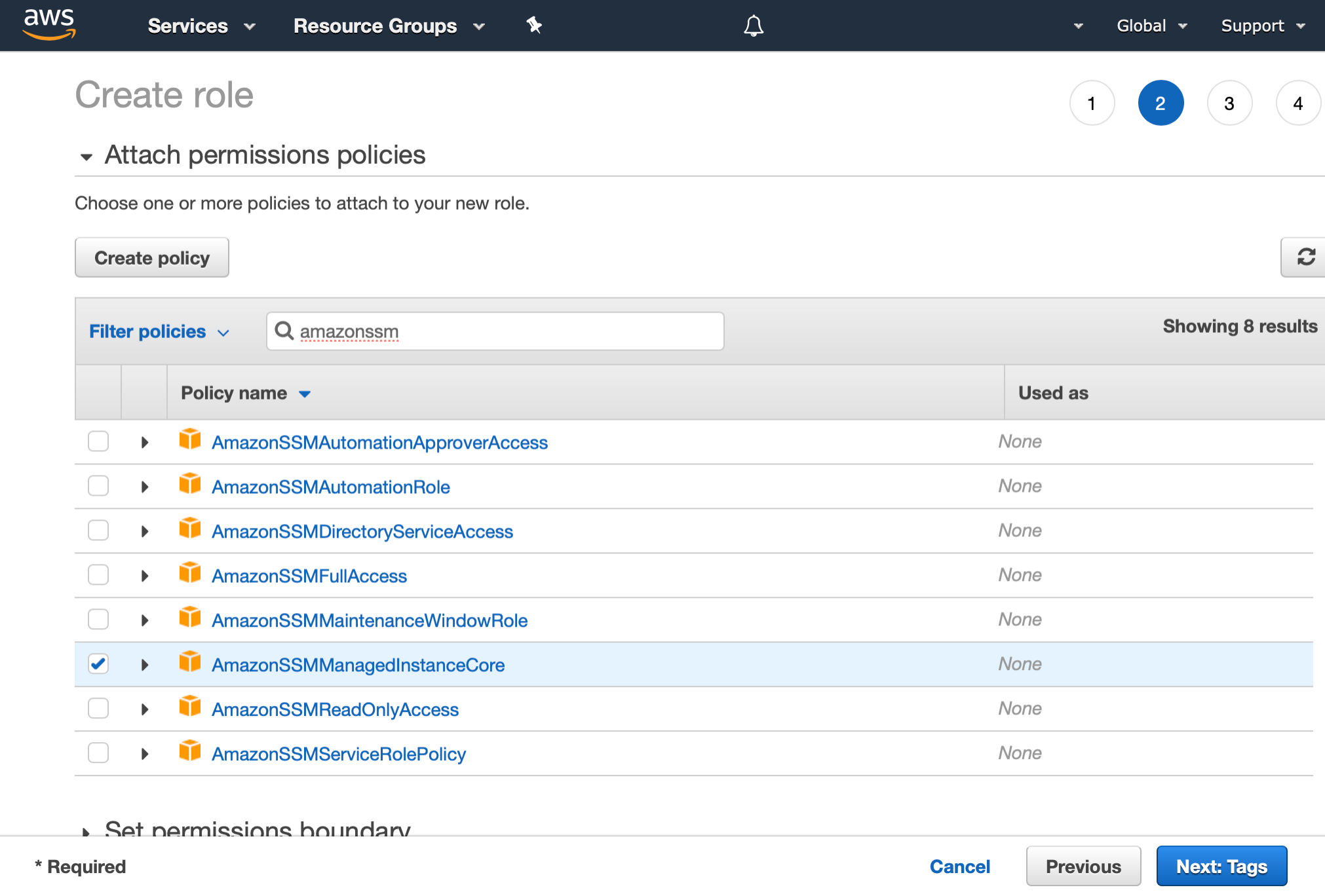
Amazonssmmanagedinstancecore permissions-To add Session Manager permissions to an existing role (console) Sign in to the AWS Management Console and open the IAM console at https//consoleawsamazoncom/iam/ In the navigation pane, choose Roles Choose the name of the role to embed a policy in Choose the Permissions tab Choose Add inline policy add permissions for Session Manager actions to an existing IAM instance profile that does not rely on the AWSprovided default policy AmazonSSMManagedInstanceCore for instance permissions assumes the existing profile already includes other Systems Manager ssm permissions for actions you want to allow access to
Shell Into An Ubuntu Instance On Ec2 From A Browser Using The Systems Manager Agent Notes From Bowers Server Geek
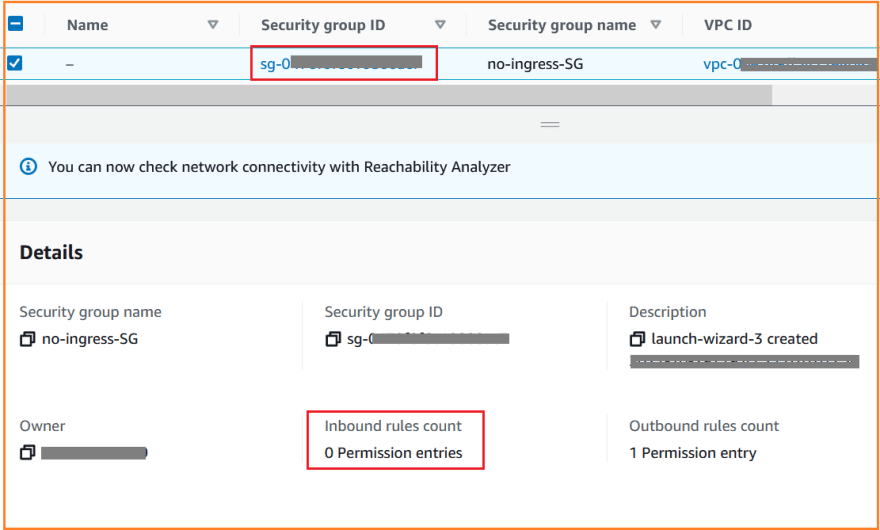
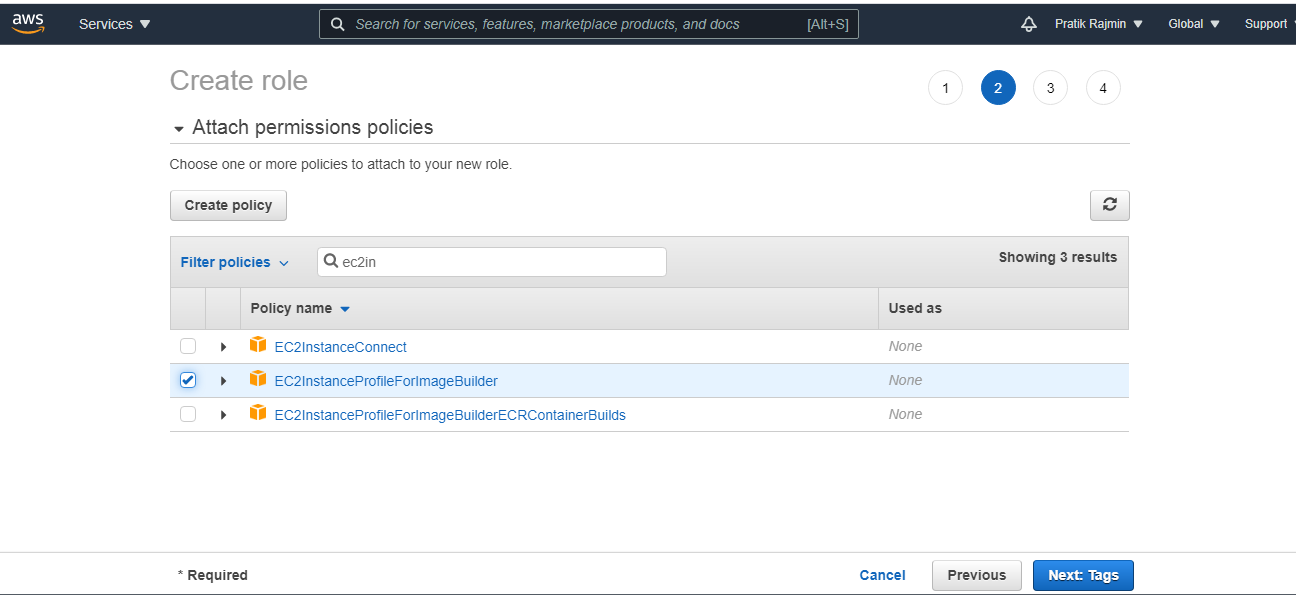
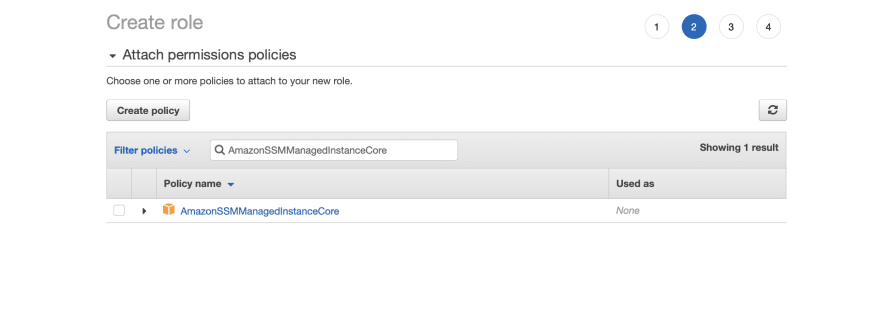
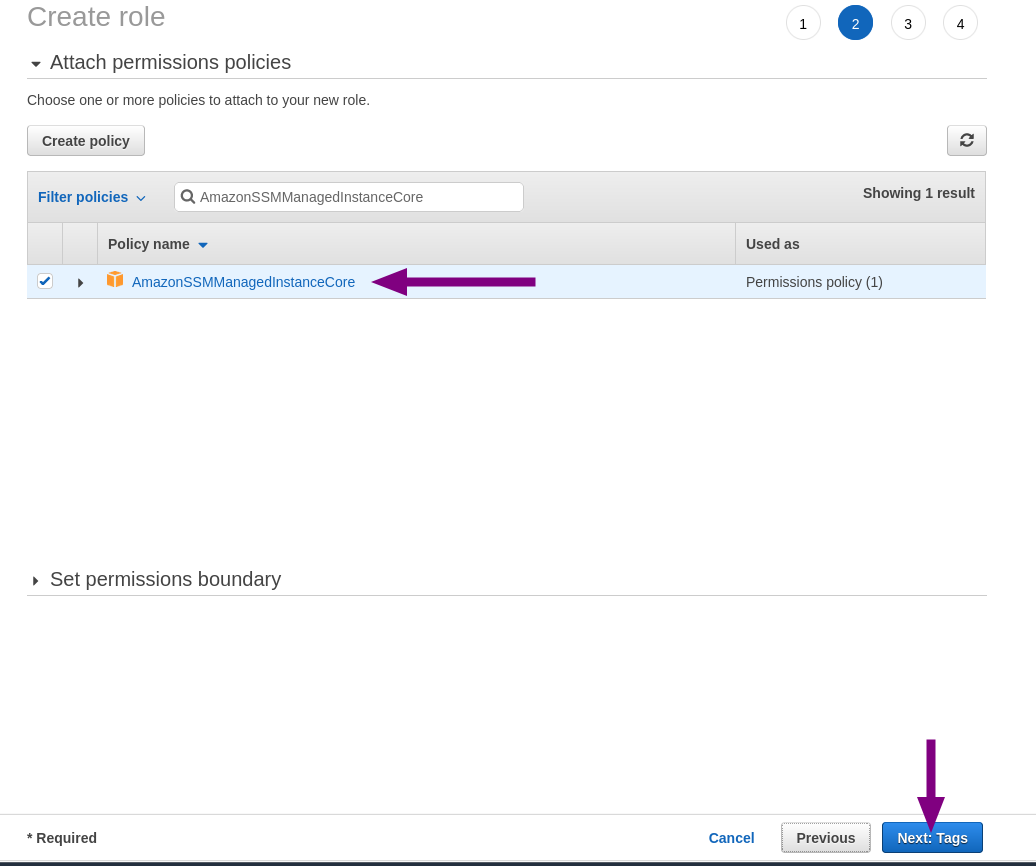
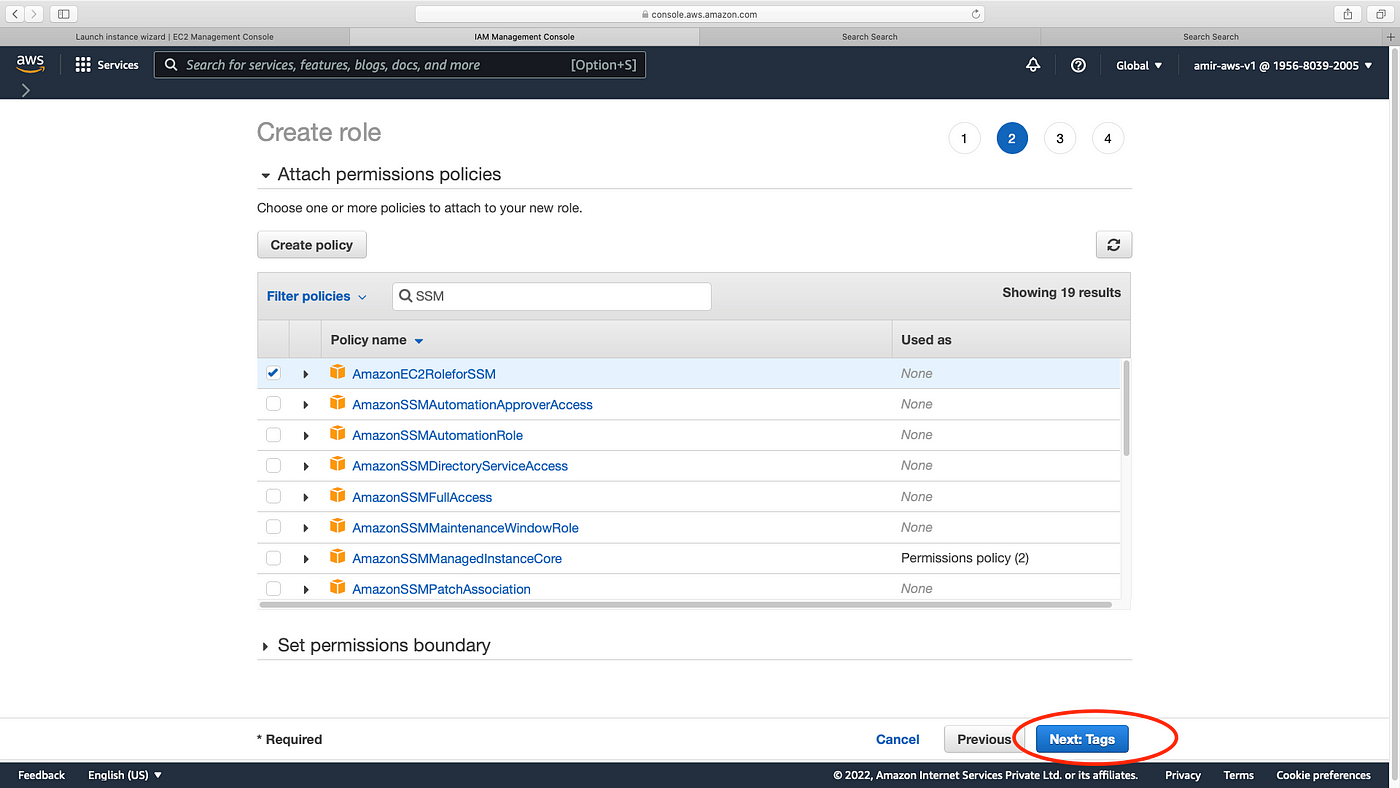
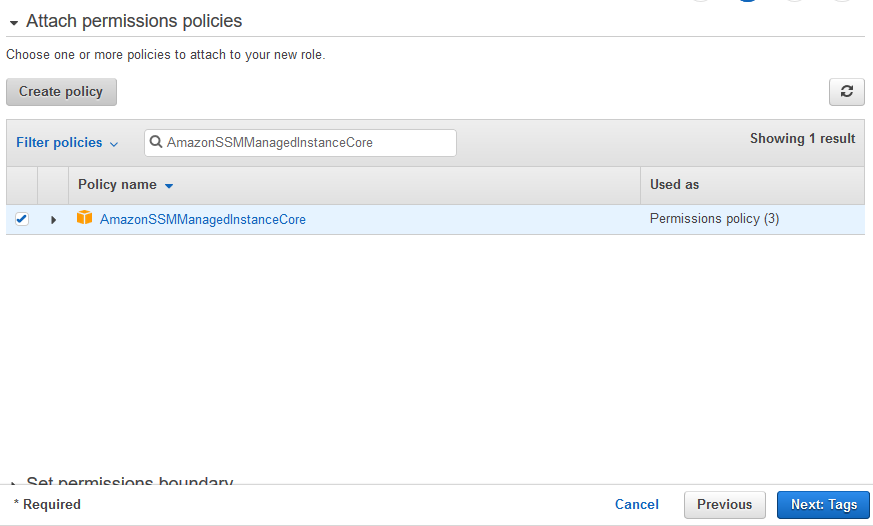
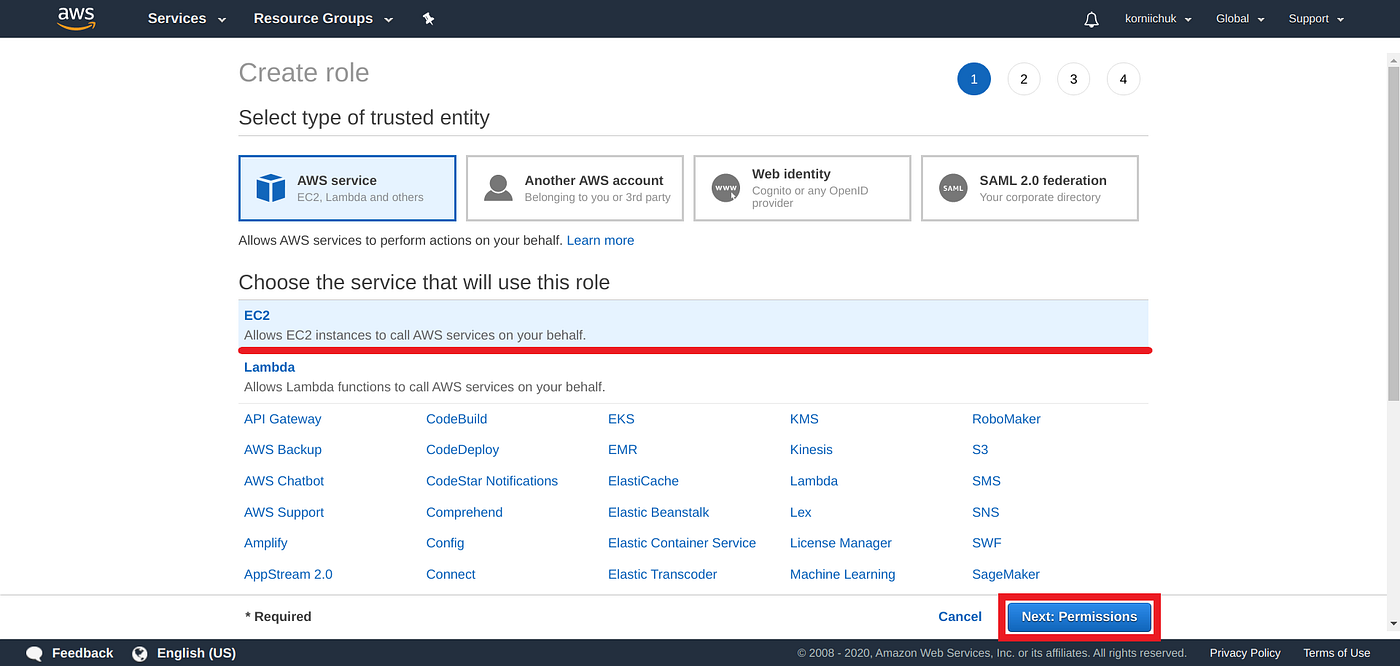
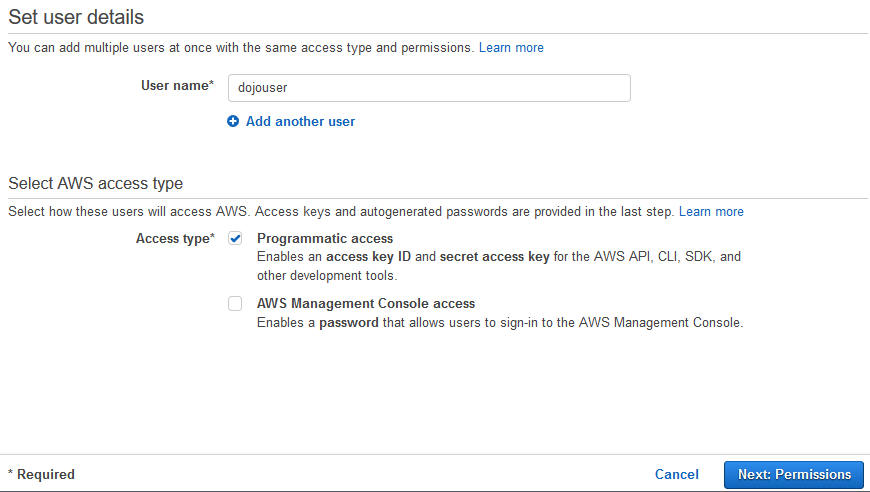
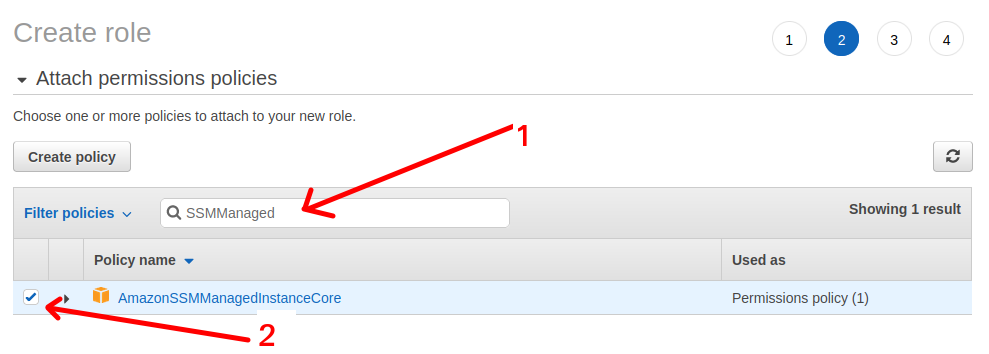
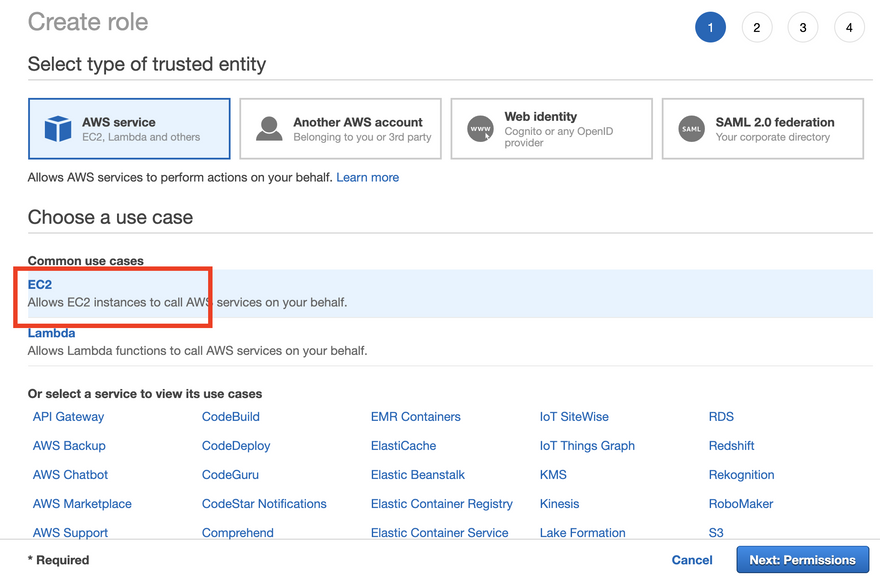
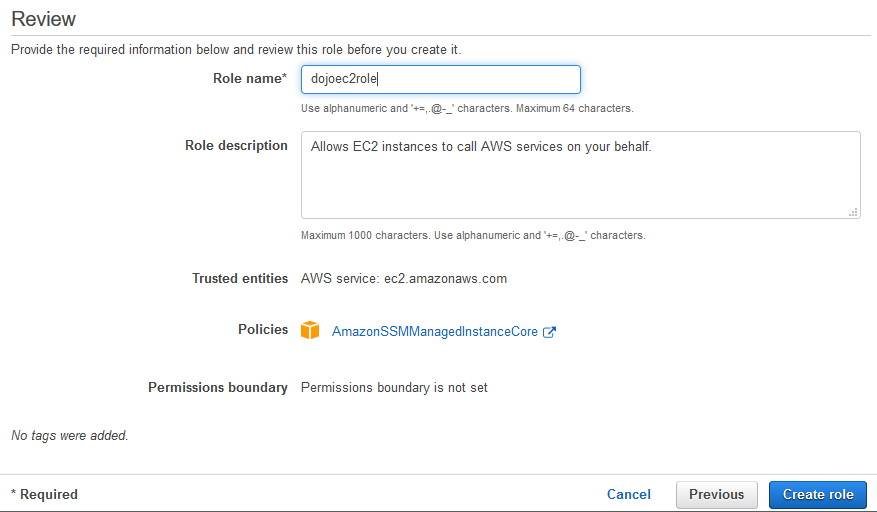
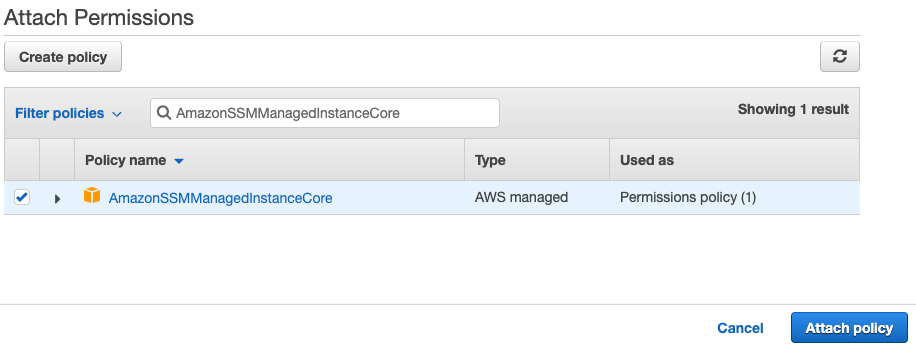
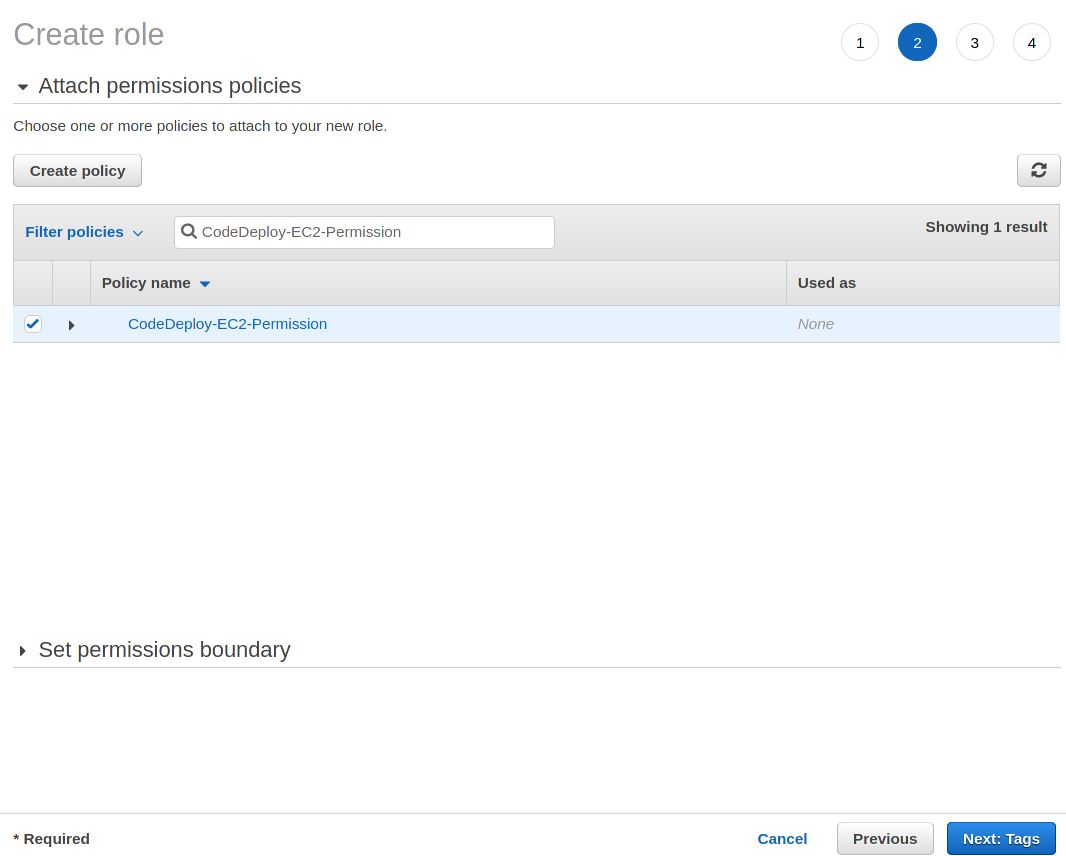
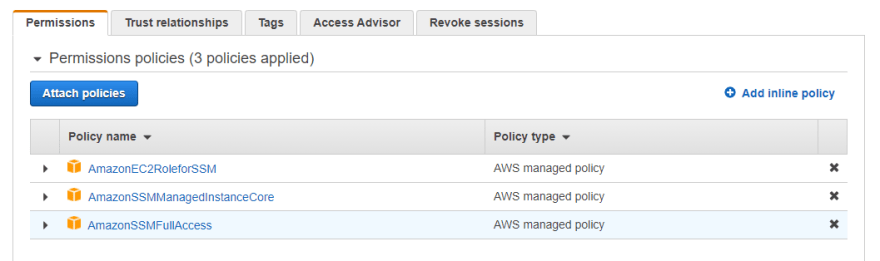
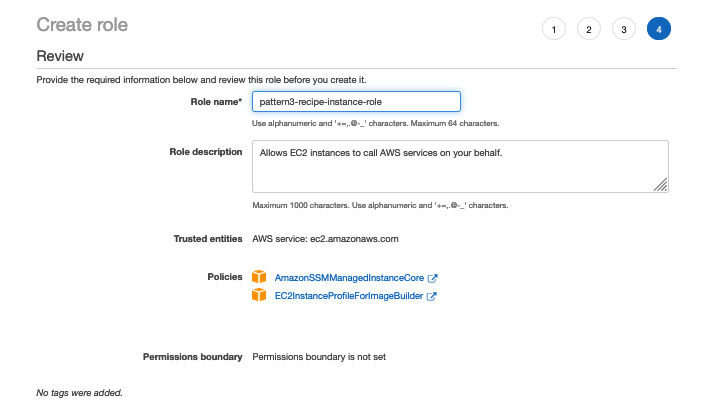
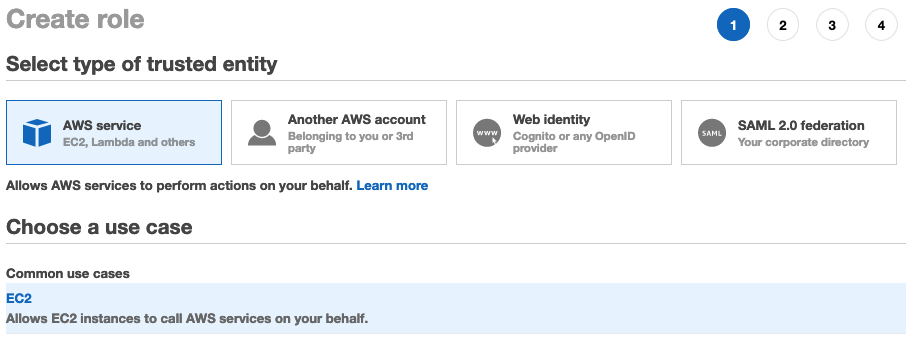
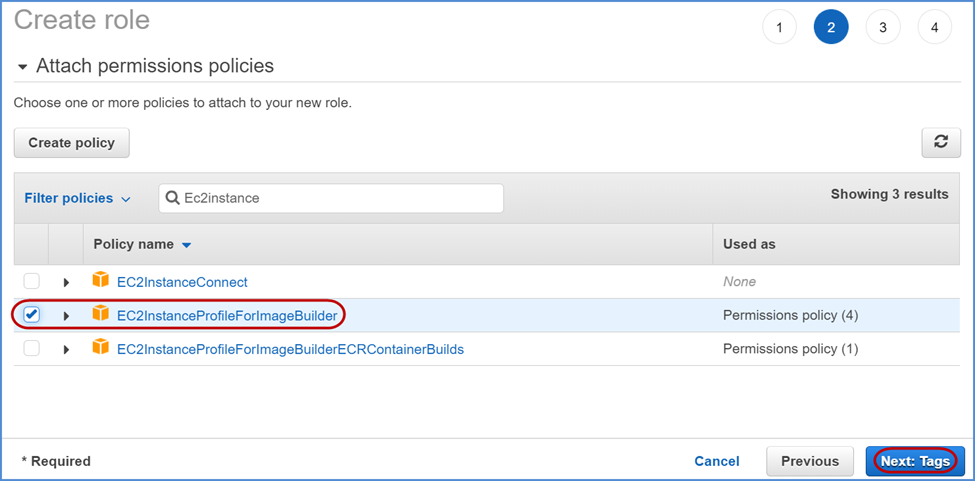
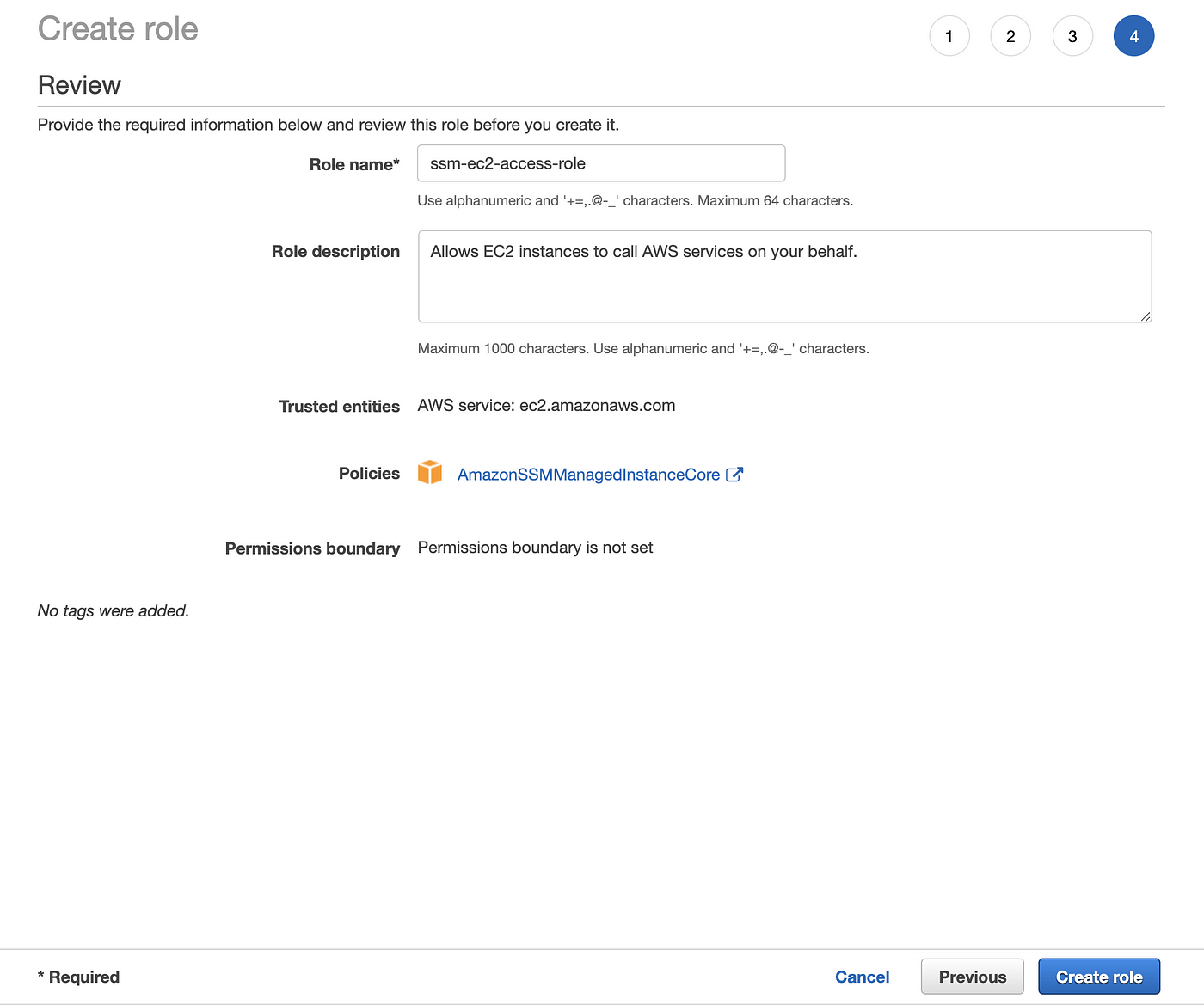
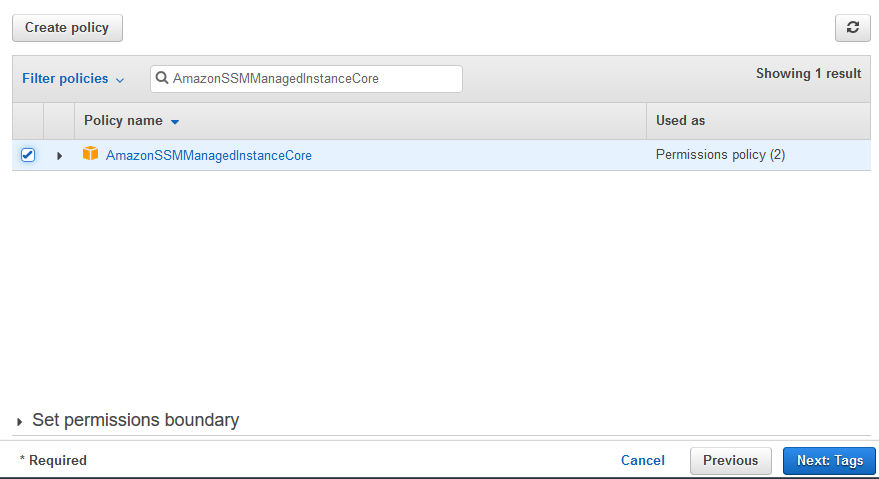
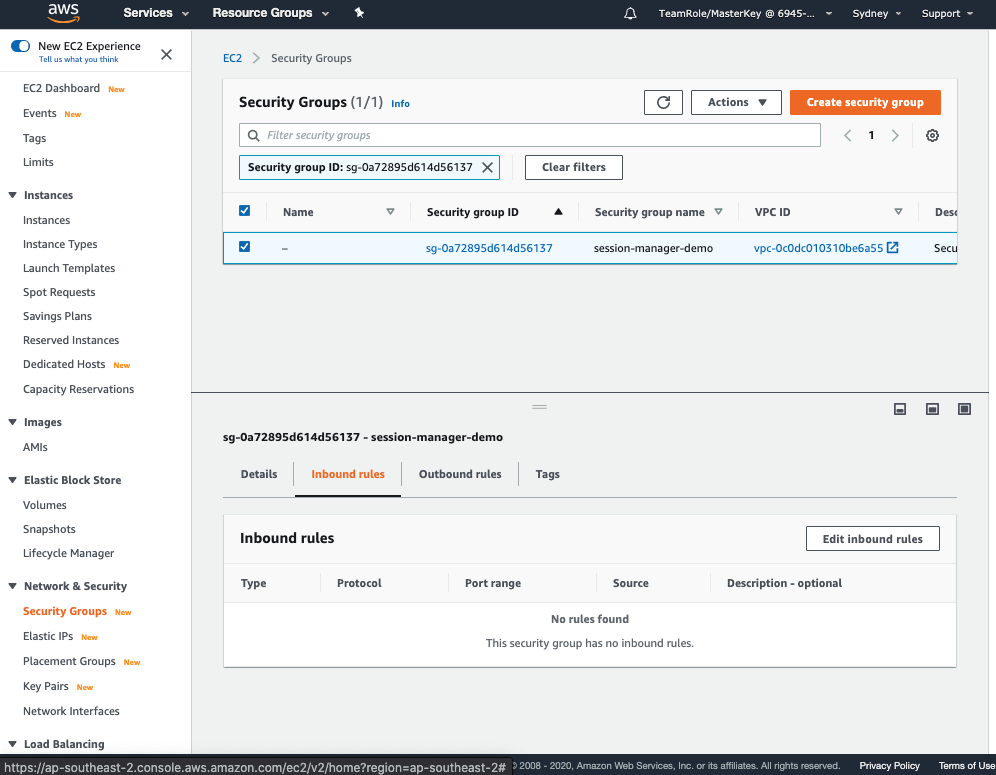
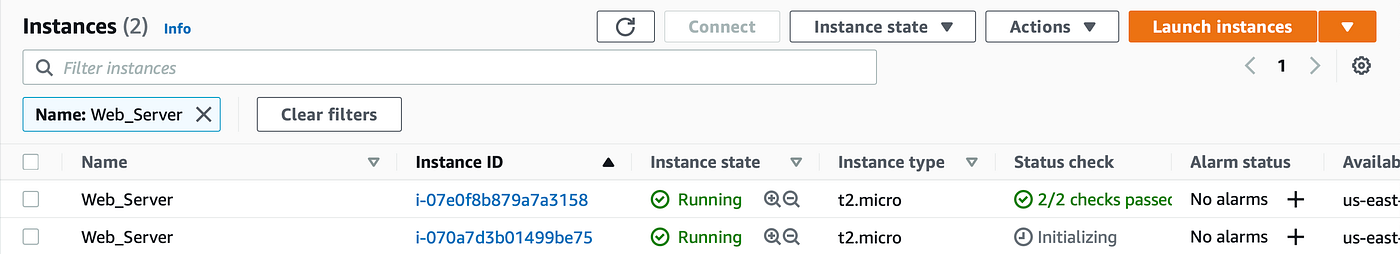
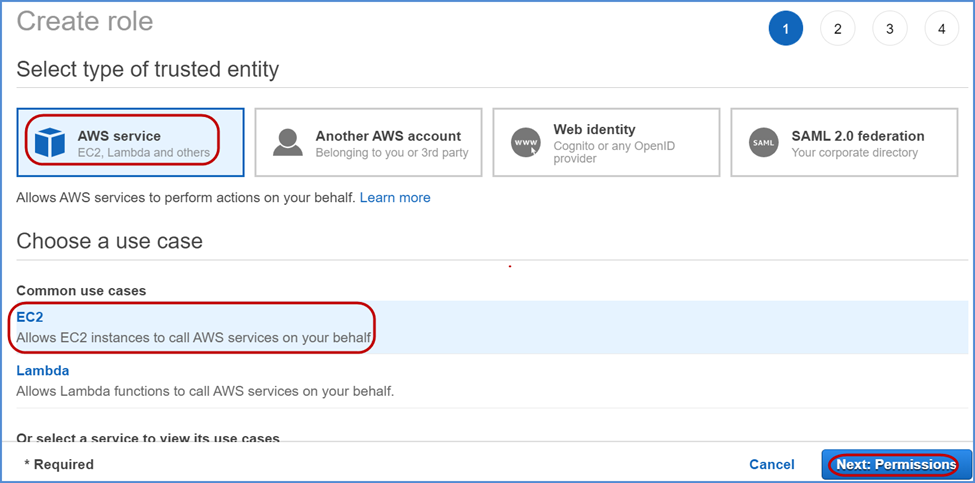
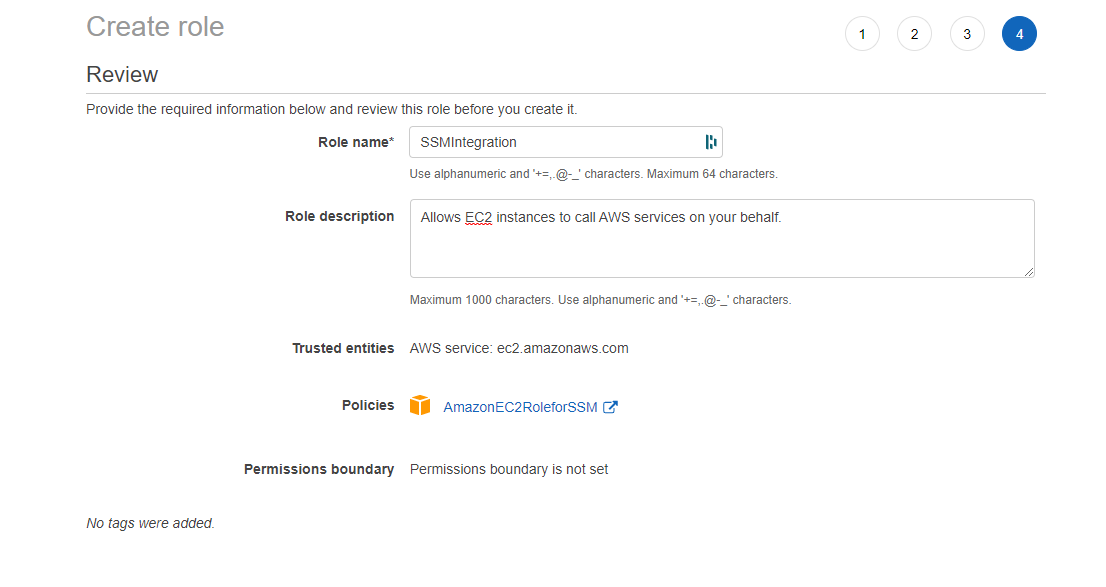
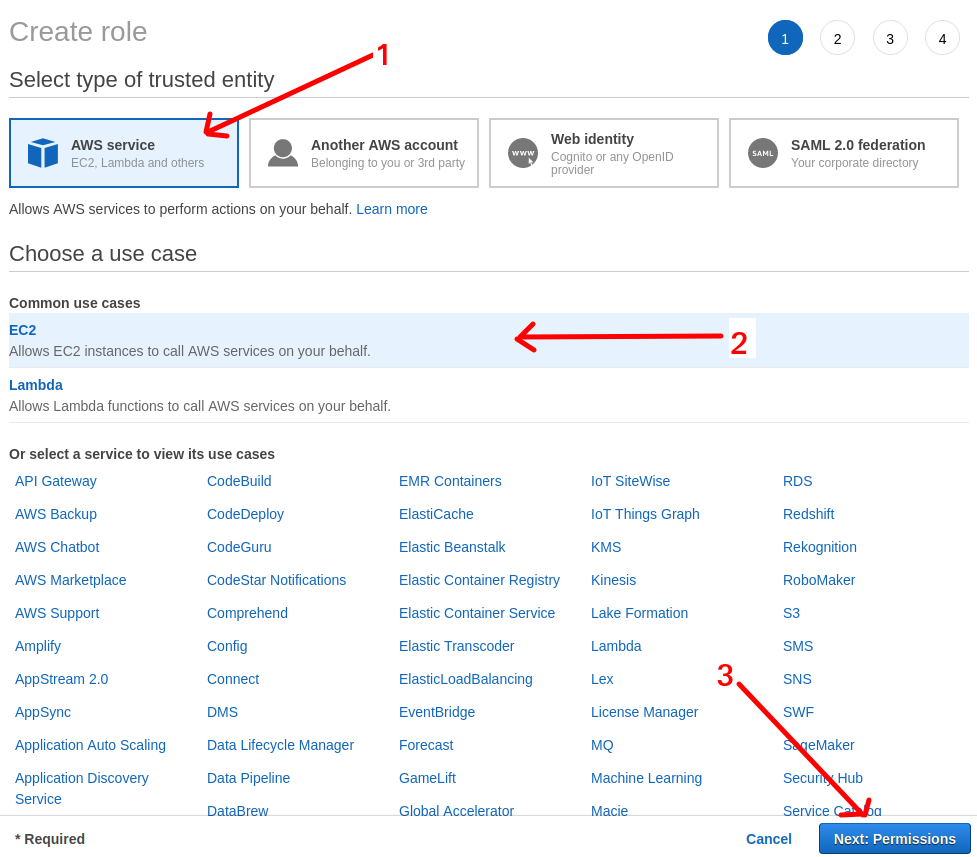
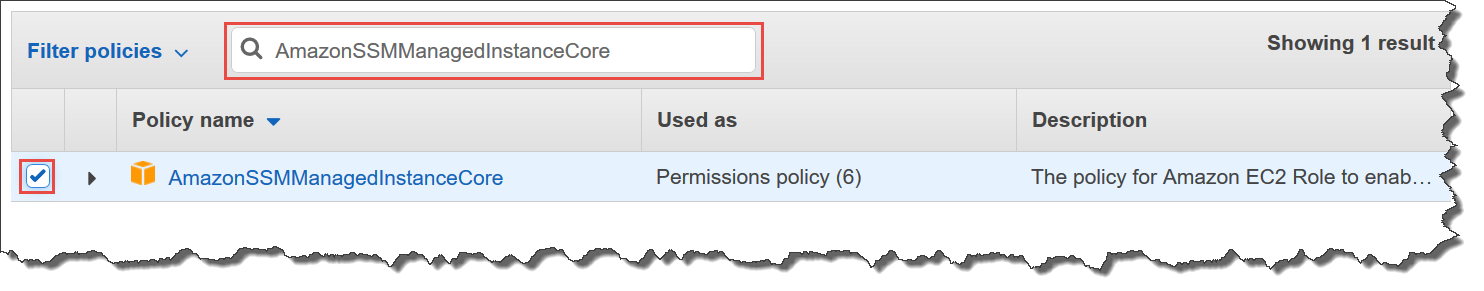
For Set permissions, choose Attach existing policies directly In the list of policies, select the check box next to CloudWatchAgentServerPolicy If necessary, use the search box to find the policy To use Systems Manager to install or configure the CloudWatch agent, select the box next to AmazonSSMManagedInstanceCore For permissions attach AWS managed policies called AmazonSSMFullAccess and AmazonSSMManagedInstanceCore Then skip tags and proceed to Review For this demo we will call our role TestSSMFullAccess STEP 2 Attach IAM Role to your EC2 Instance This demo assumes that you have an EC2 instance running already To download the JSON file from your browser, see amazon_restricted_role_permissionsjson Use default security group To use the default security group, move the toggle key to the right If you select this option, the Commvault software assigns the default security group that is defined within your VPC, instead of a specific security group for
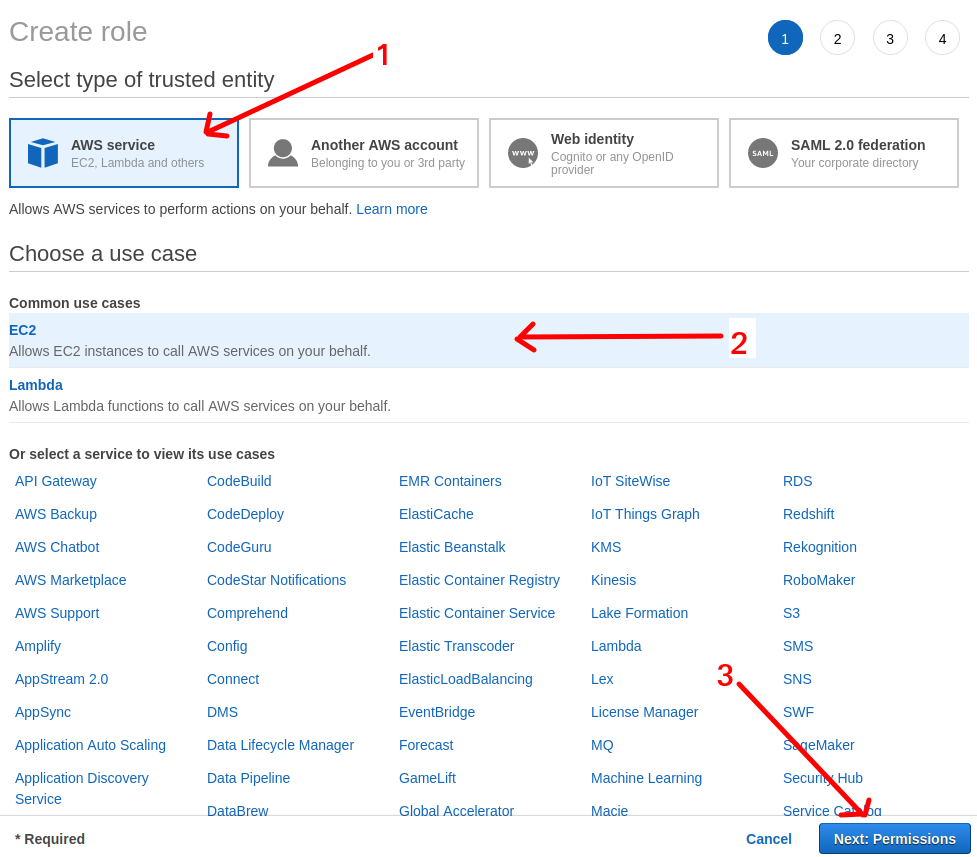
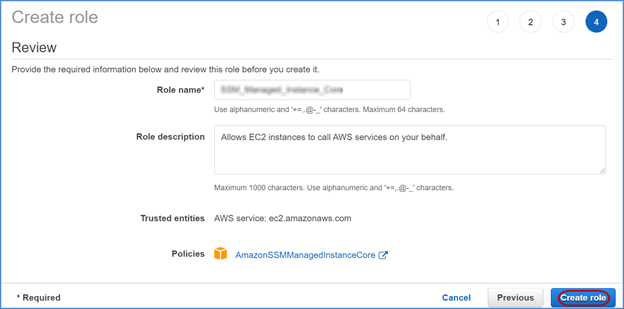
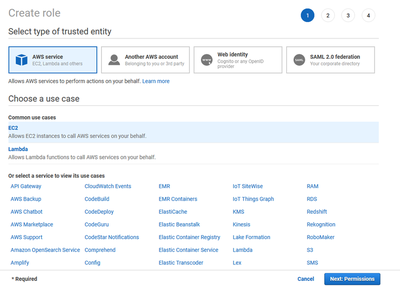
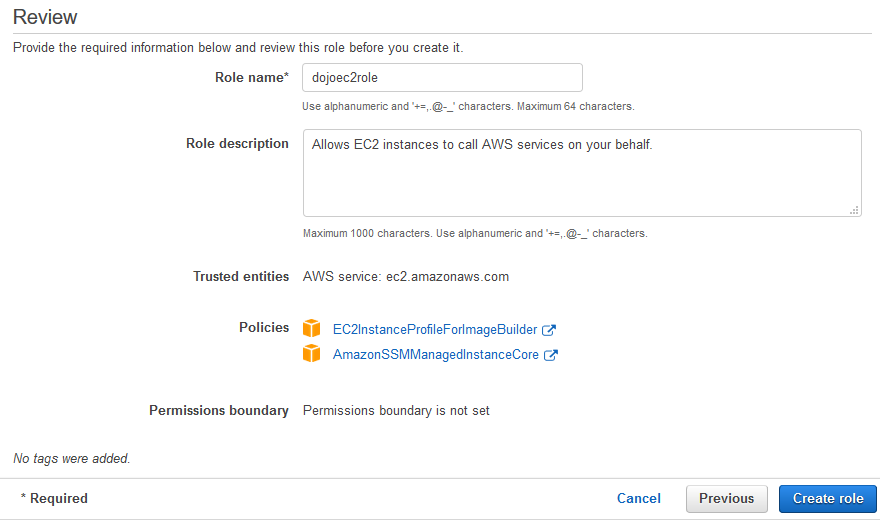
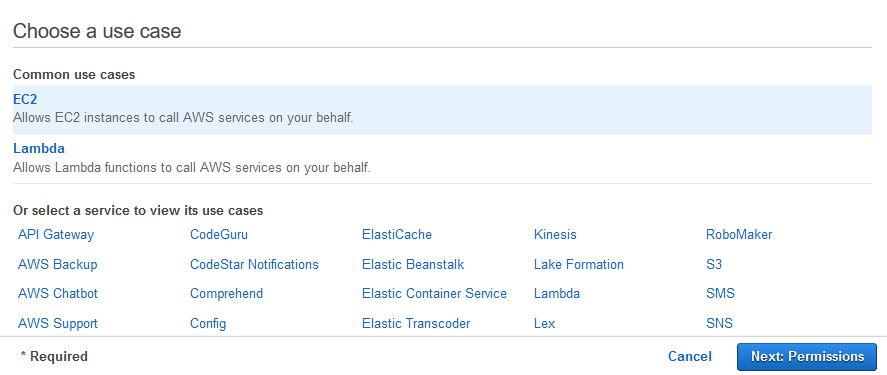
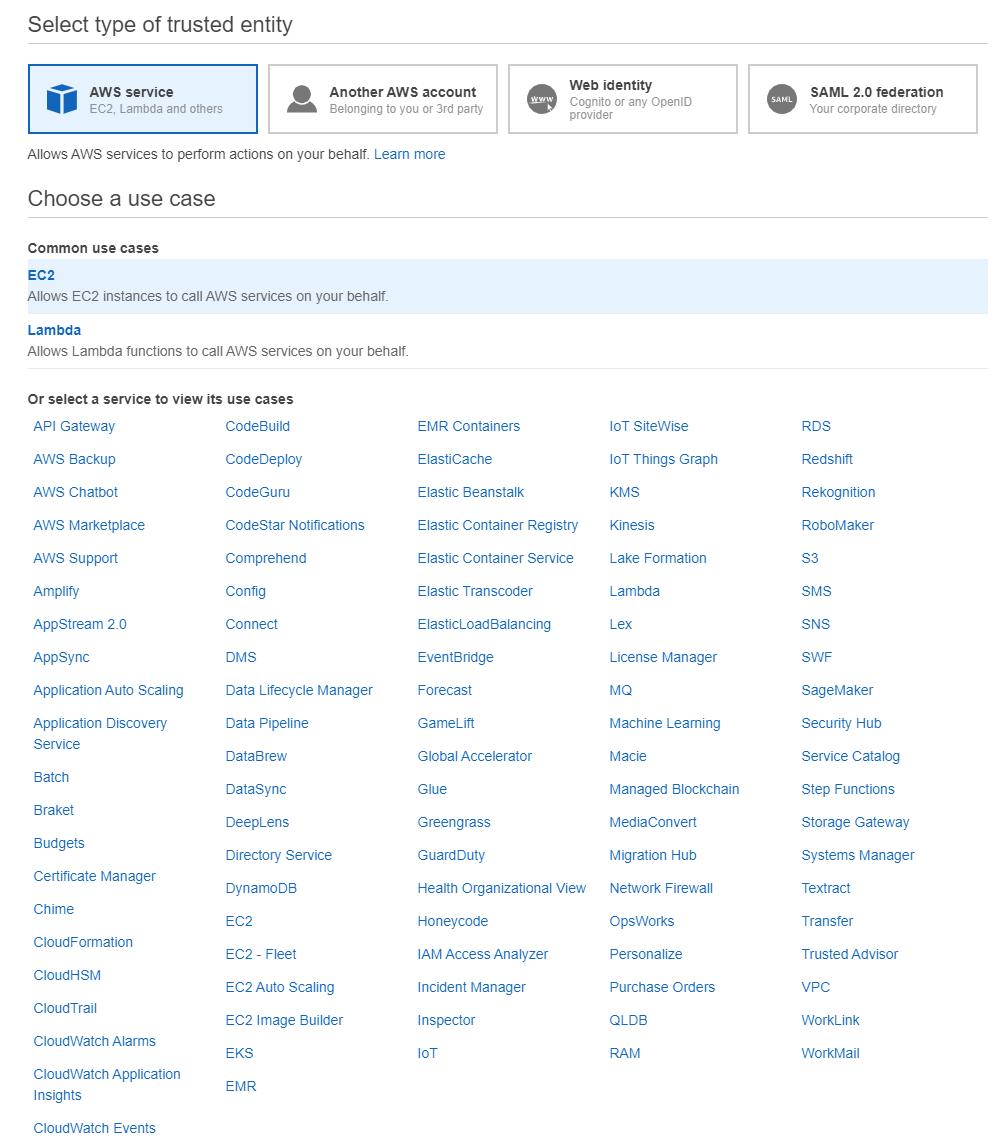
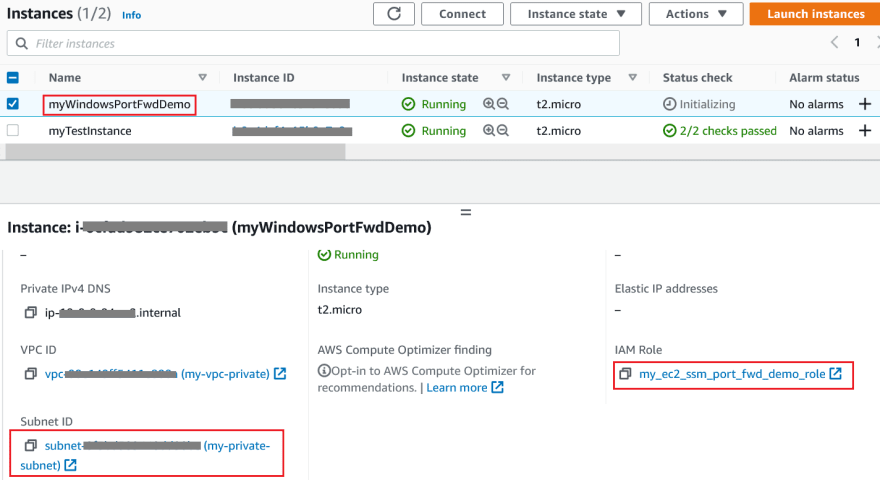
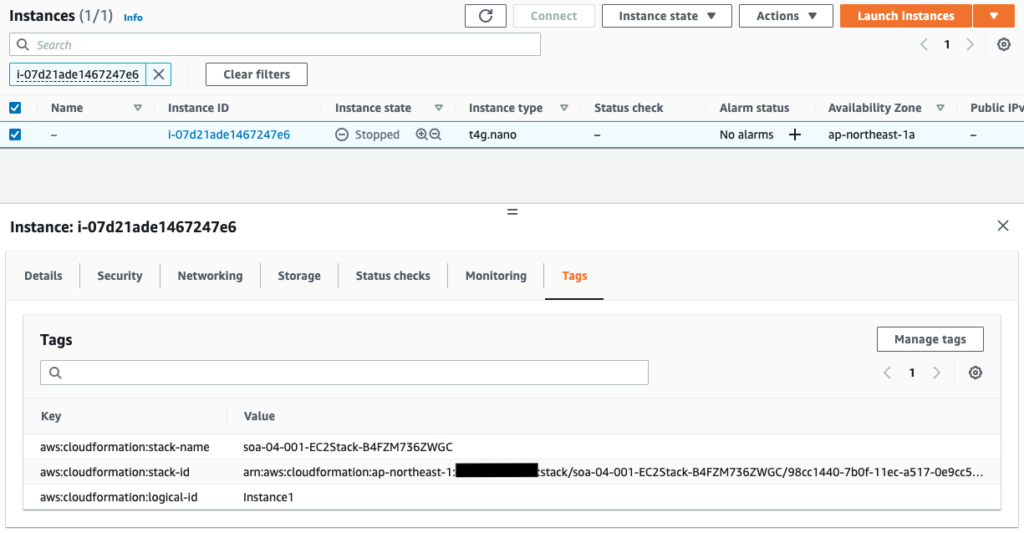
Select AWS service in Type of trusted entity, and EC2 in the common use case, then click Next Permissions In the Policy search field, search and select AmazonSSMManagedInstanceCore, then click Next s Click Next Review In the Role name field, give any name for the EC2 roleIn the navigation pane, choose Roles and then choose Create role Choose the AWS service role type, and then choose Systems Manager, Allows SSM to call AWS services on your behalf Choose the Systems Manager use case and then Next Permissions give it a name myec2ssmrole Now we have a role for the EC2 instance, next we need to add that role to the instance Go to EC2 https//consoleawsamazoncom/ec2 select your instance from the menu on the top right, select actions, security, modify IAM role select the role you just created myec2ssmrole press save
Amazonssmmanagedinstancecore permissionsのギャラリー
各画像をクリックすると、ダウンロードまたは拡大表示できます
 |  |  |
 |  | |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  | |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  | |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  | |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  | |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  | |
 |  | |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |  |  |
 |  |  |
 |  |  |
「Amazonssmmanagedinstancecore permissions」の画像ギャラリー、詳細は各画像をクリックしてください。
 |
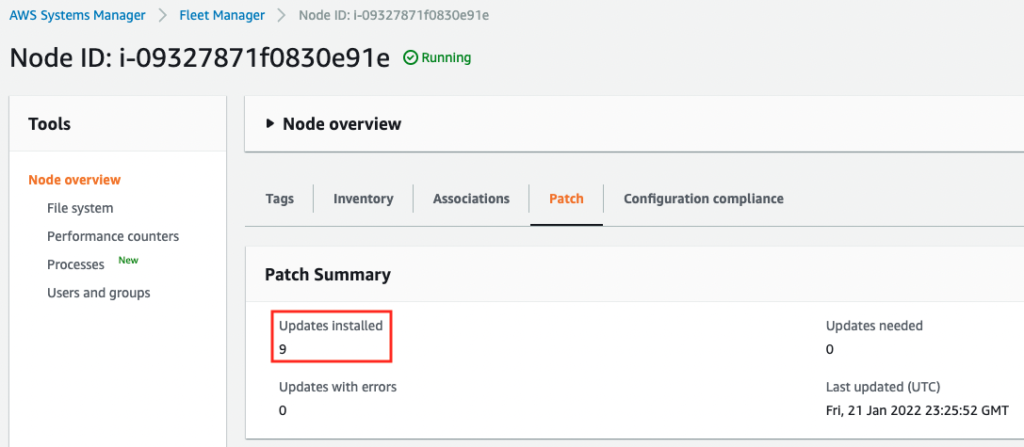
Verify that the IAM instance profile attached to the instance includes the required permissions Tried the troubleshooting methods but still getting the following error and one more thing even I removed the attached role the ec2 instance stillIf an instance profile that contains the AWS managed policy AmazonSSMManagedInstanceCore is already attached to your instances, the required permissions for Session Manager are already provided This is also true if the IAM service role used in your hybrid activation contains the AmazonSSMManagedInstanceCore managed policy Important
Incoming Term: amazonssmmanagedinstancecore permissions,




No comments:
Post a Comment